Overview
Versa Zero Trust Network Access (ZTNA) connects your users to private applications securely, regardless of location or hosting environment. It integrates seamlessly with your existing tools and apps, ensuring direct, risk-minimized access through least privilege control and continuous trust evaluation. This solution minimizes risk by dynamically adjusting security measures based on real-time analysis of user behavior and network conditions, ensuring business continuity and data integrity.
Discover how Versa ZTNA can fortify your network.
Enforce least-privilege access based on granular app, user and group policies.
User and group-based policies provide secure, granular control over application access. This ensures that only authorized users can access specific private applications.

Application-specific policies
Customize access controls for each application.
User- and group-based policies
Granular identity and group-based policies for secure access and activity controls.
Dynamic policy adjustment
Policies adapt in real-time based on user behavior and context.
Integration with IAM systems
Seamlessly integrate with Identity and Access Management systems for streamlined access control.
Adapt to evolving threats with real-time secure posture assessment
Continuous assessment of security posture allows for adaptive measures, minimizing exposure to threats. This ensures a robust defense against evolving security risks. Versa’s approach to ZTNA continually verifies users and devices, ensuring no implicit trust - regardless of location.
Continuous verification
Continuously track device security posture and user activities.
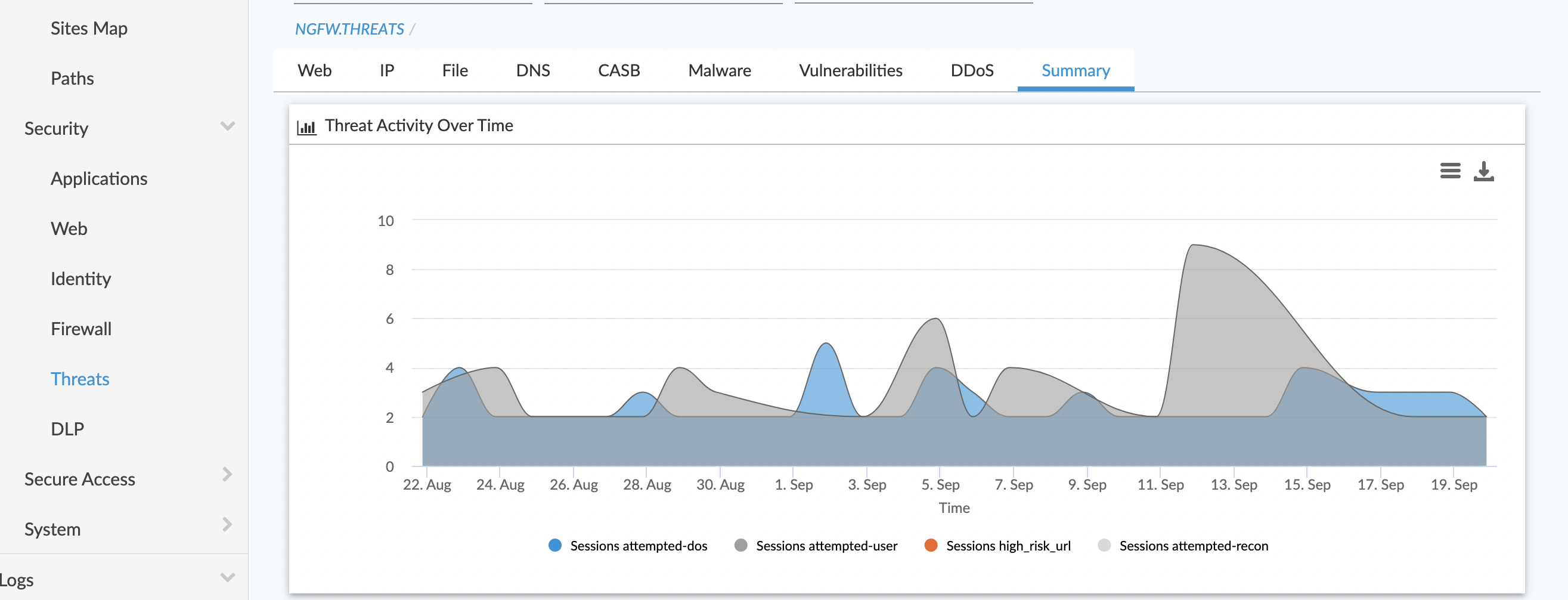
Threat detection and response
Identify and respond to threats in real time.
Stop lateral movement
Versa's adaptive micro-segmentation divides the LAN into microsegments and contains risky users and devices to eliminate lateral threat movement.
Security policies that move with the user
You can centrally manage a unified repository of granular Zero Trust policies that are consistently enforced - whether users are working at home, on the road, or connecting from an office. Not only does this simplify deployment and administration, it reduces complexity and improves your security posture.

Policy follows the user
Ensure security policies are consistent whether users are on-premises or remote.
Continuously assesses security posture
Regularly evaluate and adjust security measures.
Adaptive security policies
Dynamically change policies based on real-time context.
Integrates with identity providers
Work seamlessly with multiple identity management systems.
VPN replacement
Replace VPNs and enhance your security posture with least privilege access controls for both remote and on-premises users.
Consolidate ZTNA, CASB, SWG and DLP
Upgrade and consolidate ZTNA, CASB, SWG, and DLP under a uniform deployment, configuration and reporting platform.
Dynamic protection
Adjust security measures in real time to counter threats when accessing private applications.
Solution Briefs
Solution Brief
Securing Digital Transformation Initiatives with Versa Secure Internet Access (VSIA)
Read NowAnalyst Report
White Papers
White Paper
How Adopting A Zero Trust Architecture Can Help Protect Against Digital Supply Chain Management Attacks
Read NowWhite Paper
Simple Do’s and Don’ts to consider when transitioning from a legacy VPN solution to a remote ZTNA solution
Read NowBlogs
Blog
Versa Achieves Exceptional Results in CyberRatings.org SSE Threat Protection and ZTNA Tests
Read NowBlog
Data Defense in Depth: Unifying Data Protection and Zero Trust through SASE for Ultimate Data Protection with Versa Networks
Read NowBlog