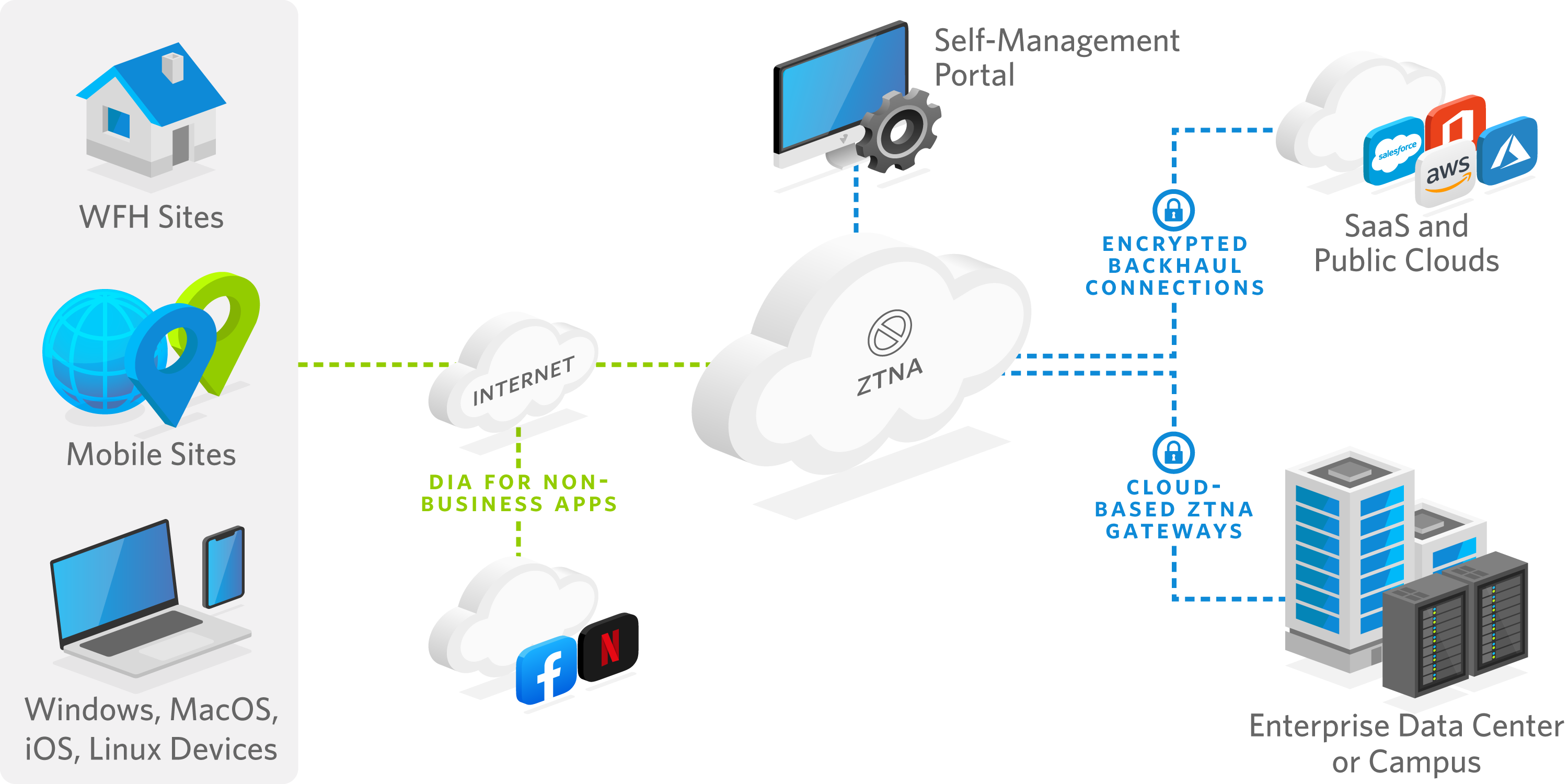
How Does ZTNA Work?
ZTNA is a client-to-application—not network-centric—approach to authenticate security based on:
-
the identity and context of the user, and
-
the device and application (or any other asset) being accessed
The ZTNA security broker verifies each access attempt regardless of location. It applies corporate policy and grants granular, least-privilege access to an asset (an application, URL, data or other destination). A ZTNA architecture:
- Regards the network as providing only transport, and makes no architectural difference between on-prem and off-prem users, devices or applications/assets.
- Applies consistent corporate policies to all asset access attempts regardless of the entity (user, device, and application/asset) requesting the access, or the location of the entity or the requested asset.
- Provides full security for all WFA users, on any device, for any on-prem or cloud application.
- Segments the network end-to-end to ensure granular access for legitimate users only to applications allowed within their privilege credentials.
ZTNA architecture comprises several components:
- SDP broker/proxy: Makes outbound-only connections to ensure both the network and the applications are invisible to unauthorized users; the broker may be an appliance or a cloud service.
- Cloud Gateway: Cloud-deployed, globally distributed gateways securely connect to the enterprise network and cloud/SaaS destinations.
- Client: SASE client software for end-user devices. A clientless deployment is also available.
- Authentication services: Interacts with the enterprise’s existing user and device credential management and authentication service.
- Self-management Portal: Provides administrative visibility and control of users and applications.
- Transport: Wired, wireless, or cellular internet or intranet connections.