How Versa Secures Unstructured Data Against AI-Driven Risk

June 17, 2025
The proliferation of AI and machine learning workloads has accelerated the generation and utilization of unstructured data—including emails, source code, collaboration files, logs, recordings, and internal documentation. Unlike structured data, which resides in databases, unstructured data spreads across cloud drives, SaaS applications, endpoints, and unmanaged collaboration tools.
This data is valuable for training AI models, powering copilots, and enabling advanced analytics. But for security teams, it’s a growing attack surface—often outside existing DLP or segmentation strategies.
What makes this trend particularly urgent is the active data interaction via generative AI tools (e.g., ChatGPT, Claude, Copilot, Gemini). These tools are increasingly becoming integral to workflows—but they operate in ways that bypass traditional controls, ingest sensitive content, and can introduce privacy, IP, and compliance risks.
Security Risks and Compliance Violations: Unsecured Unstructured Data
Cybersecurity managers now face a scenario where unstructured data can be:
Ingested by AI services
(intentionally or accidentally) and become part of unauthorized model training.
Accessed by Shadow AI tools
—unauthorized AI applications not sanctioned by IT.
- Exfiltrated via browser, API, or unmanaged devices, bypassing perimeter controls.
Exposed to prompt injection and adversarial AI
that manipulate inputs or retrieve unintended information.
Stored or cached in SaaS applications
where data residency and retention are opaque.
These risks translate to data breaches, regulatory violations (e.g., GDPR, HIPAA, CCPA, ISO27001), and potential loss of competitive IP.

Versa’s Approach to Secure Unstructured Data for AI
Versa provides an integrated security platform that enables cybersecurity managers to monitor, control, and protect unstructured data access, even in distributed and AI-driven environments. Here’s how each security pillar of Versa Unified SASE contributes:
1. ZTNA – Granular Access Control by Identity, Context, and Risk
Versa’s ZTNA enforces least-privilege access to data sources, including collaboration platforms, internal wikis, file shares, and developer repositories. Policies are dynamically enforced based on:
- User identity (via SSO integration)
- Device posture (via EDR integration)
- Real-time risk scoring (behavioral, geographic, anomaly-based)
This ensures that only compliant users and devices can access sensitive data—and blocks unauthorized AI agents or extensions attempting lateral movement. Further combined with Versa’s DLP, it provides real-time in-line protection against data exfiltration. Try Versa Unified SASE : ZTNA here
2. CASB – AI SaaS Discovery and Shadow AI Policy Enforcement
Versa CASB inspects cloud app usage and flags unsanctioned AI services which can be applications, websites and copilots. It enables:
- Discovery of AI SaaS tools in use (e.g., ChatGPT, Notion AI, Jasper)
- Risk scoring and app classification
- API-level enforcement (block, quarantine, redact) for sensitive data
For sanctioned apps, policies can be applied to govern what data types can be submitted (e.g., source code, PII, financial records), ensuring controlled AI usage. Try Versa Unified SASE : CASB here
3. SWG – Data-Aware Web Access Control with AI Guardrails
Versa’s cloud-delivered SWG provides in-line HTTP/S inspection, allowing real-time control over data egress. Key protections include:
- AI-specific URL filtering and content inspection
- Context-aware upload restrictions
- Regex, fingerprint, or ML-based detection of sensitive unstructured data
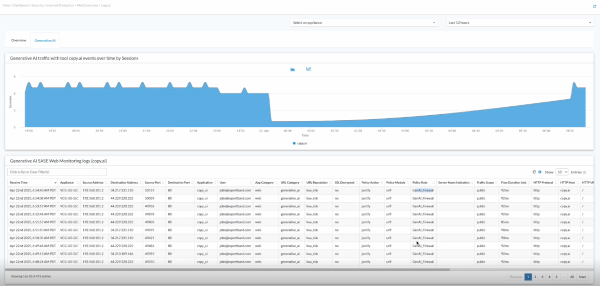
Administrators can create granular rules to block prompts that contain confidential information or watermark outbound data submissions to AI interfaces.
4. FWaaS – Unified L4-L7 Security at Scale
Versa FWaaS provides centralized control over north-south and east-west traffic, including encrypted sessions. It supports:
- Deep packet inspection (DPI) for application-layer enforcement
- Segmentation of AI workloads and user traffic
- TLS inspection for encrypted AI API traffic (e.g., OpenAI, Anthropic, Azure ML)
Firewall policies can detect AI tool usage over non-standard ports or tunneling behavior from extensions, ensuring full-spectrum visibility.
5. Versa’s ATP stack protects against evasive, AI-generated threats, including:
- Malware obfuscated via LLMs
- Prompt injection attempts
- Adversarial queries that target internal content
- AI bots scraping accessible web-facing unstructured data
ATP is integrated with threat intel feeds and applies behavior-based analytics to detect anomalies in how users or tools interact with data.
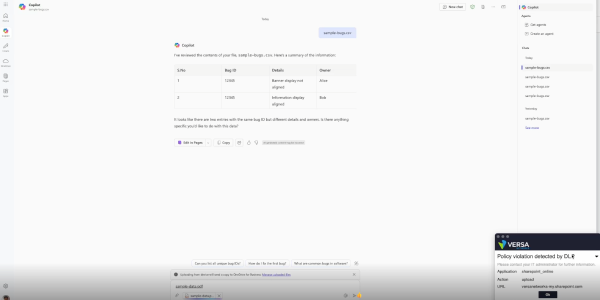
6. DLP – Multi-Modal Unstructured Data Classification and Protection
Versa’s DLP inspects data in motion, in use, and at rest—across file uploads, emails, web forms, and cloud sync events. It supports:
- Pattern-based detection (PII, PCI, PHI, custom regex)
- NLP and ML-driven classification of documents and images
- File fingerprinting and policy enforcement (block, encrypt, quarantine)
DLP policies can be tailored to flag data inserted into AI tools, even when obfuscated or encoded, offering last-line defense for unstructured content.
Operational Benefits for Cybersecurity Teams
Versa’s converged architecture unifies policy enforcement across all user traffic—whether accessing data from managed endpoints, remote locations, or through AI-driven cloud services. By combining identity, device, and network context with deep content inspection and real-time analytics, Versa enables cybersecurity teams to enforce data-centric policies across the entire digital estate without the overhead of stitching together point solutions.
Key benefits include:
Reduced attack surface
for unstructured data accessed via AI tools, browsers, APIs, or SaaS apps.
Unified policy management
across web, network, cloud, and private application access—minimizing operational complexity.
Real-time incident response and forensics
with full audit trails of data access, exfiltration attempts, and risky behavior across AI tools.
Audit-ready compliance
with DLP templates and access logs mapped to regulatory frameworks like GDPR, HIPAA, ISO 27001, and NIST 800-53.
Tight integration
with existing security operations via APIs for SIEM/SOAR ingestion, endpoint telemetry sharing, and threat intelligence feeds.
Adaptive risk controls
where suspicious behavior (e.g., excessive data access from unmanaged AI tools) can trigger automated policy changes or user isolation.
This gives security teams full-spectrum visibility and control over data interactions without compromising user productivity or data agility.
Next Steps
The security perimeter no longer ends at the endpoint or the app—it extends to the prompts, models, and AI tools interacting with your data. Versa equips security teams to close this visibility and control gap. For full experience try a 2-min self-guided product walkthrough and schedule a detailed technical demo with team.
Subscribe to the Versa Blog
Recent Posts
Versa SASE Fabric
By Matthew BrooksMay 26, 2026
What Enterprises Are Really Saying About AI Security
By Dan MaierMay 14, 2026




