The WAN for AI-era applications is becoming a single system

April 23, 2026
Dell’Oro: Distributed cloud networking emerges as ‘the WAN for AI-era applications’ – SDxCentral
Dell’Oro Group is putting a sharper name on something enterprise teams have been feeling for a while: in the AI era, the “WAN” cannot be a collection of loosely coupled products anymore. It has to operate like one end-to-end system with one policy model, one telemetry story, and one operational workflow across:
- User edge (branches, users, endpoints)
- Middle mile (the fabric/backbone between edges)
- Application edge (SaaS, cloud, private apps)
That is the essence of the “distributed cloud networking becomes the WAN” framing that was highlighted: buyers are moving beyond isolated upgrades and instead prioritizing architectural alignment. In plain terms: “Does this behave like a system?” is replacing “Does this feature exist?”.
Why AI-era traffic breaks fragmented WAN designs
AI does not just add “more traffic.” It changes the shape of traffic and the expectations around it:
- Apps are more distributed (SaaS + public cloud + private apps + edge services)
- Traffic becomes more variable (bursty, multi-region, latency-sensitive)
- Telemetry explodes (more signals to correlate across network, security, and experience)
In a fragmented environment with Secure SD-WAN here, security somewhere else, visibility in a separate tool the outcome is predictable:
- triage gets slower,
- operations gets more expensive,
- and policy becomes inconsistent across paths.
The new buying test is simple:
Can you keep user-to-app experience stable and secure while paths and policies change dynamically—without stitching together three stacks?
A quick clarification: VSAF is not “only the middle mile”
A common mistake in these discussions is to treat the middle mile as the product.
Versa Secure Access Fabric (VSAF) is not just “the middle mile.” It is the end-to-end Secure Access Fabric construct. Within that construct, the SASE Fabric is the portion that behaves like the “middle mile”: the Secure SD-WAN-powered fabric connecting global cloud gateways/PoPs and enabling consistent policy and performance-aware steering across those enforcement points. The VSAF integrates security into the fabric to provide east-west security for traffic traversing the network.
That distinction matters because “convergence” is not about building a better backbone, it is about operating networking + security + experience as one system.
How Versa maps cleanly to Dell’Oro’s three pillars
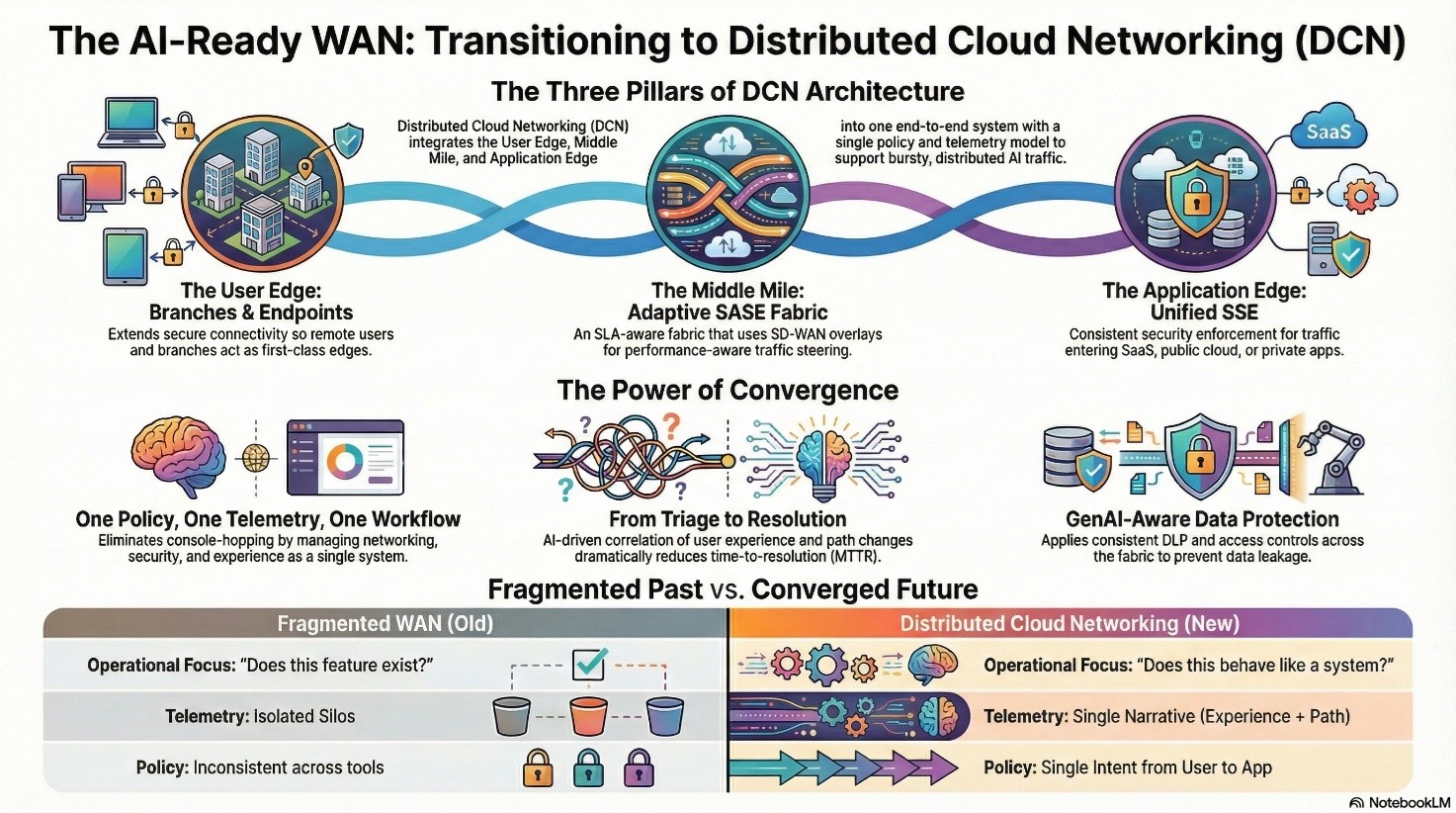
Here is the clean mapping of Versa Networks to the user edge / middle mile / application edge rubric.
1) User edge: Secure SD-WAN + endpoint turns every user into a first-class edge
At the user edge, the goal is consistent connectivity and segmentation whether the “edge” is a branch or a remote user.
- Branch Secure SD-WAN edge enforces app-aware routing and segmentation.
- Endpoint client extends secure connectivity into the fabric so remote users behave like first-class edges, not a special case that forces exceptions and workarounds.
2) Middle mile: an SLA-aware SASE Fabric that is adaptive by design
This is where the WAN stops being “tunnels” and starts behaving like a fabric:
- Full-mesh connectivity between cloud gateways using Secure SD-WAN overlays
- SLA-aware traffic engineering that chooses paths based on performance and application needs
- Continuous performance measurement and distribution of performance intelligence back to edges so decisions improve over time and are made in real time based on current network status
- Optional optimization/acceleration techniques (like TCP optimization, Forward Error Correction) where they materially help
The outcome is a middle mile that is not static, it is measured, adaptive, and intent-driven.
3) Application edge: SSE controls where traffic meets SaaS/cloud/private apps
At the application edge, the value isn’t “security exists”; it is security that is consistent and operationally unified.
- Cloud gateways provide the enforcement points for SSE controls for Internet/SaaS and private app access.
- Policies remain consistent as traffic exits to SaaS/cloud or enters private apps—without a separate stack and separate workflow.
4) End to End Telemetry: Service Assurance from User to Applications
Distributed Users connecting to distributed applications require continuous monitoring of user performance, application performance and network performance. Traffic steering and routing policy decisions need to be made dynamically based on current performance experience and application requirements.
- Secure SD-WAN Branches, Cloud Gateways and Versa clients continuously monitor, measure and inform the performance to their peers.
- Secure SD-WAN devices and Cloud Gateways use Traffic Engineering principles to ensure that traffic flows over most optimal paths towards the destination.
What “convergence” really means in practice
Dell’Oro’s convergence point is ultimately an operations thesis:
- One policy model: the intent does not change as traffic moves from branch → fabric → SaaS
- One telemetry story: you can explain outcomes with a single narrative (experience + path + enforcement)
- One workflow: troubleshooting and change management don’t require three consoles and three teams
In the AI era, this is the difference between:
- “We cannot tell if it is the network, the security hop, or the SaaS provider,” and
- “We know exactly what changed, where, and what to do next.”
Where AI belongs: reducing time-to-resolution across the whole fabric. AI is most defensible when it reduces operational cost across the end-to-end system, not when it is bolted onto a silo.
High-value AI outcomes look like:
- Faster “why is this app slow?” triage by correlating user experience, path changes, and enforcement outcomes
- Smarter recommendations for steering or policy changes because the system has unified telemetry
- GenAI-focused protections that actually matter because enforcement is consistent at the same fabric enforcement points not unevenly applied across disconnected tools
In other words: AI gets powerful when it is optimizing a single system with a single telemetry plane.
Three concrete examples (Automation, Security, then Governance)
Example 1 – Automation: closed-loop remediation for SaaS performance
A regional set of users reports Microsoft 365 is slow, but the SaaS provider status page is green. The fabric can automatically correlate (a) user experience drop, (b) path latency/jitter changes in the middle mile, and (c) enforcement outcomes at the application edge. If it detects a degraded path or overloaded gateway, it can auto-steer traffic to a healthier gateway or alternate underlay, validate the improvement, and attach the full context to a ticket (what changed, when, and the remediation that was applied) without a war room.
Example 2 – Security: GenAI-aware data protection with consistent enforcement
A user attempts to paste a sensitive customer dataset into a GenAI tool. The same fabric enforcement point that provides access can apply inline controls: classify content, enforce DLP policy (block, redact, or coach), and log the event with user identity, device posture, and destination context. If the attempt is anomalous (new device, unusual geo, high-risk behavior), the system can trigger step-up authentication, isolate the session, and open an incident with a clear root-cause narrative (who, what data, which app, and what control fired).
Example 3 – Governance: policy intent and auditability across edges
A new AI-enabled app is introduced and teams start accessing it from branches and unmanaged devices. Instead of creating separate policies across Secure SD-WAN, SSE, and endpoint tools, governance can start from a single intent: who can access the app, from which device posture, and what data controls apply. The system can generate a change plan (blast radius, affected segments, rollback), require approval via RBAC, and continuously audit for drift so the policy stays consistent everywhere.
Optional extension: SD-LAN completes the “single thread” inside the branch
If you want the story to go all the way to the first hop, SD-LAN extends the same intent-driven model inside the branch/campus so identity, segmentation, and policy start before traffic even hits the WAN edge.
That yields the cleanest “single thread” narrative: endpoint to LAN segment to Secure SD-WAN to SASE Fabric (middle mile) to SSE enforcement to application
The takeaway:
Versa’s Secure Access Fabric aligns with the DCN thesis: Secure SD-WAN and secure access at the user edge, an SLA-aware SASE Fabric as the middle mile between global cloud gateways, and SSE controls at the application edge operated through a unified portal and increasingly optimized with AI.
Call to action:
If you are prioritizing Automation and Security (and then Governance), here are three practical ways to start:
1) Automation: pick your top 3 ‘experience killers’ (e.g., Microsoft 365, Zoom, Salesforce) and define what ‘good’ looks like (latency, loss, app response time). Automate detection + steering + ticket enrichment as a closed loop.
2) Security: define your GenAI control posture – which tools are allowed, which data types are never allowed (PII, source code, regulated data), and what the user experience should be (block vs coach vs redact). Enforce consistently at the fabric enforcement points.
3) Governance: add guardrails – require change approval (RBAC), auto-generate blast radius and rollback plans for policy updates, and continuously audit for drift across branch, remote, and cloud gateways.
Want to pressure-test your architecture against the Dell’Oro DCN rubric?
Bring one application and one recent incident (for example: ‘SaaS slowdown’ or ‘GenAI data leakage’). We will map the end-to-end policy + telemetry + remediation path across user edge, middle mile, and application edge and identify the first two automations that will materially reduce MTTR and risk.
Subscribe to the Versa Blog
Recent Posts
Versa SASE Fabric
By Matthew BrooksMay 26, 2026
What Enterprises Are Really Saying About AI Security
By Dan MaierMay 14, 2026



