
Artificial intelligence is transforming how work gets done, but it’s also reshaping the threat landscape. Attackers are increasingly using AI to automate reconnaissance, discover vulnerabilities, and generate new malware and phishing campaigns at scale. All this has led to a dramatic rise in zero-days targeting enterprises.
At the same time, the browser has become the de facto workspace. Employees access SaaS applications, collaborate in real time, and rely on generative AI tools all through the browser.
This combination of AI-accelerated threats and a browser-centric work environment has made the browser the primary enterprise attack surface, making Remote Browser Isolation (RBI) an essential security control.
In this blog, we’ll explore three key security use cases for Versa RBI and how its native integration with Unified SASE strengthens overall security posture.
AI-driven attacks enable adversaries to create new variants of malware and phishing content at scale. Traditional security tools typically rely on signatures and known threat indicators. While essential, these methods may miss new or previously unseen threats, allowing a “patient zero” to introduce malicious code into enterprise environments.
RBI eliminates this risk.
Versa RBI executes every web session in a secure remote environment, ensuring that no active web content runs on the user’s device. Even if a website contains unknown malware or a zero-day exploit, it remains isolated from the endpoint and the corporate network. This approach also reduces user exposure to malicious content, including phishing pages designed to capture credentials or sensitive data.
Versa RBI complements existing security tools and is especially valuable in AI-driven threat environments attackers rapidly generate new variants designed to evade signature-based detection.
Flexible Rendering for Security and Usability
Versa RBI supports two rendering modes, allowing administrators to balance security and user experience:
Admins can apply different rendering modes based on risk level, user role, or website category. Granular action controls further ensure strong protection without sacrificing usability.
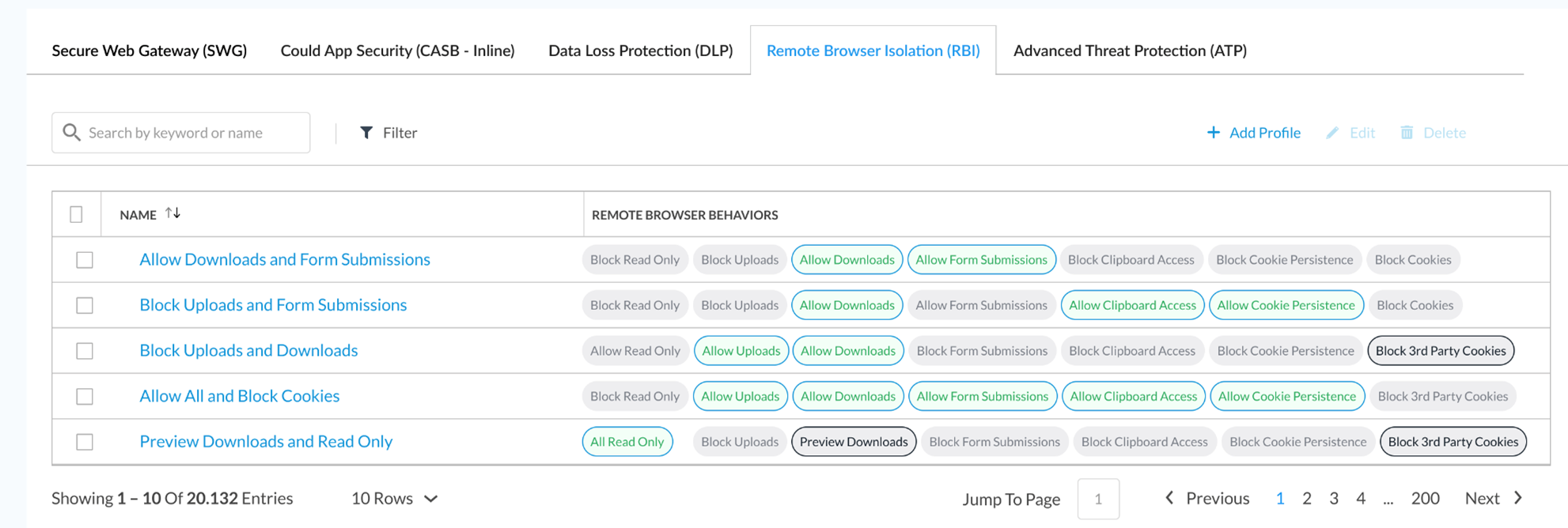
Figure 1. Granular action controls give admins control over specific actions within uploads, downloads, and submissions.
Secure File Handling with CDR
Versa RBI also enables safe file access through Content Disarm and Reconstruction (CDR).
Admins can allow file downloads but only through Versa CDR. CDR strips potentially malicious content from files and delivers a safe, reconstructed version. For example, websites may be rendered as read-only, or a user downloading a file may receive an inert PDF preview instead of the original.
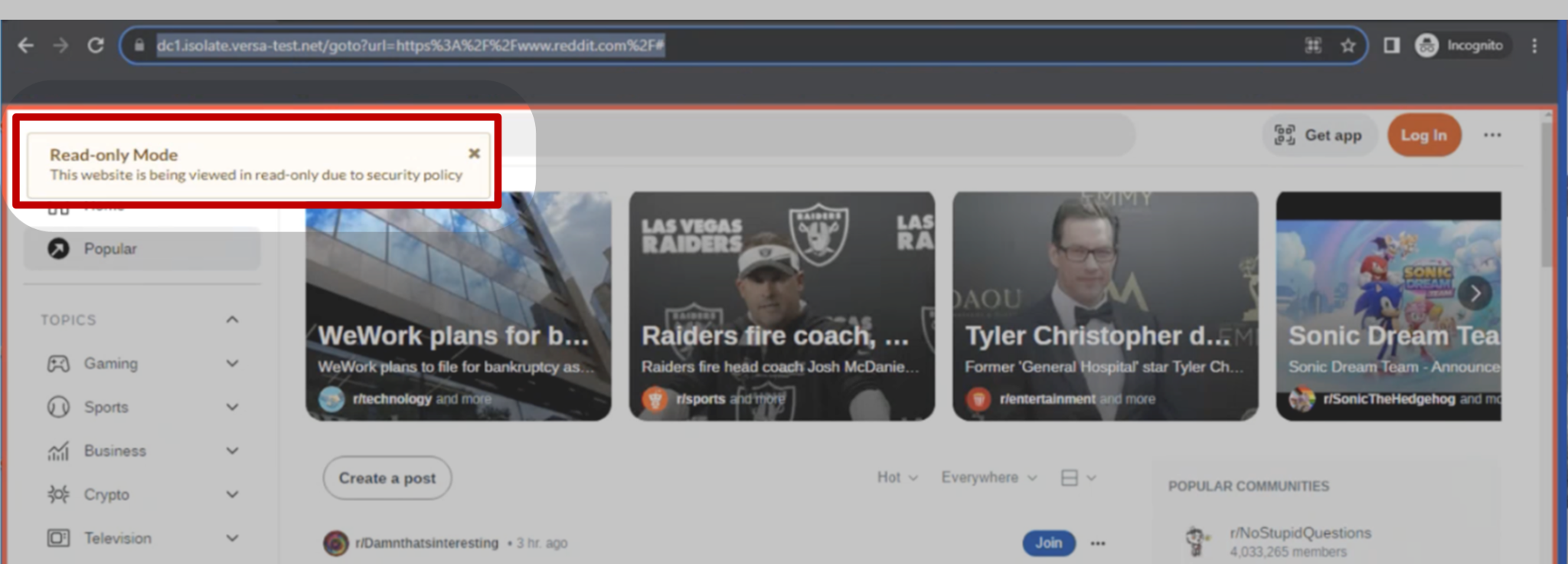
Figure 2. Entire web pages can be sanitized by rendering as read-only.
Versa RBI can also sanitize multimedia content, such as rendering videos as pixels to prevent embedded threats.
Integrated Security with Advanced Threat Protection
Versa RBI integrates natively with Secure Service Edge (SSE) capabilities, including Advanced Threat Protection (ATP).
This means inline security inspection continues even within isolated sessions.
For example:
This inline approach ensures consistent security enforcement across all browsing activity.
Generative AI tools are quickly becoming part of everyday workflows. Employees use them to summarize documents, generate code, and draft communications.
However, this convenience introduces a data exposure risk as users may unknowingly submit sensitive corporate data to external AI platforms.
Versa RBI helps reduce this exposure through native integration with Data Loss Prevention (DLP).
Administrators can control whether users are allowed to upload, paste, or interact with web applications and AI tools through RBI policies. But because Versa applies inline inspection across the platform, DLP protections remain active even during isolated sessions. So, if content violates data classification, compliance, or other DLP rules, the action is still blocked.
For example:
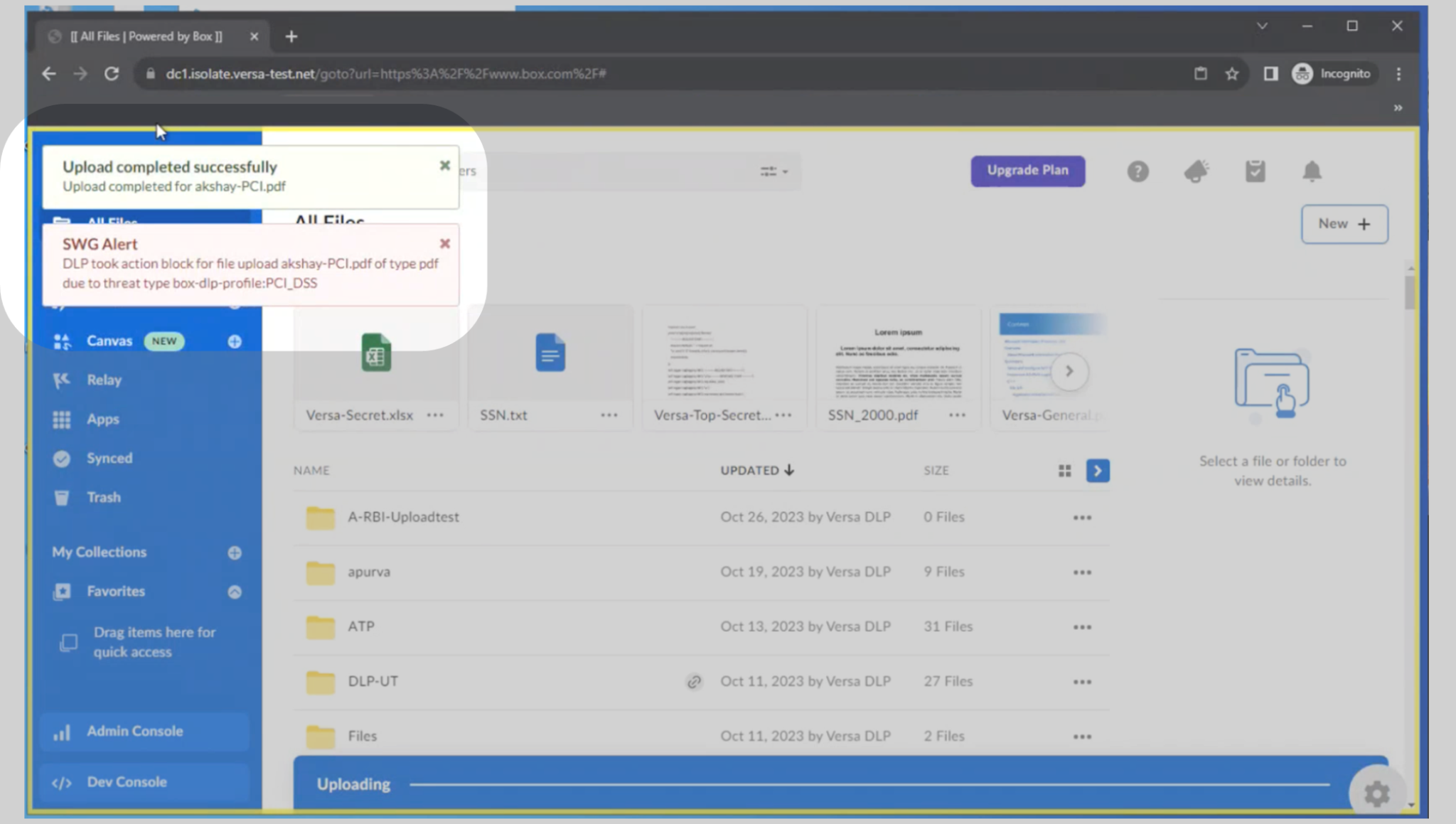
Figure 3. RBI policy allows uploads, but integrated DLP policy blocked the upload due to a PCI data violation.
This ensures sensitive information remains protected without limiting access to productivity tools.
Contractors, partners, and BYOD employees represent a growing and often under-secured segment of the workforce. Because organizations don’t own these workers’ devices, traditional endpoint agents and enterprise security controls can’t be deployed on them, leaving security gaps.
Versa RBI addresses this challenge by securing the browser session. Because web sessions run in a remote isolation environment:
By securing browser interactions, Versa RBI closes the largest entry point for threats on devices outside enterprise control, making it an effective way to support secure remote work without compromising security standards.
Versa RBI is delivered through Secure Web Gateway (SWG) controls as a native component of the Versa Unified SASE platform. A shared policy infrastructure and single management plane span security and networking components including ZTNA, CASB, DLP, ATP, and SD-WAN, eliminating policy gaps, management overhead, and security blind spots. The result is stronger protection with fewer tools and simpler administration.
As AI-assisted attacks grow more sophisticated and the browser becomes where work gets done, RBI delivers practical, high-impact protection across users, devices, and locations.
Schedule a demo to explore how Versa RBI can strengthen your security architecture.
Subscribe to the Versa Blog