Closing the Cloud Security Posture Management Gap with Versa CSPM

May 6, 2026
Today’s environments span multi-cloud infrastructure, SaaS ecosystems, remote endpoints, and an increasing layer of AI-driven applications and integrations. This expansion has introduced a new class of challenges—not just scale, but visibility.
Most organizations today have visibility in security questions around access and connectivity. They can identify who accessed which application, supported by mature identity and access telemetry, that provides visibility into user sessions, devices, and authentication context. They can also determine whether a connection was secure, using controls that inspect traffic, enforce encryption, and validate trust at the point of access.
However, this clarity fades when shifting from access to posture. Far fewer organizations can answer which cloud configurations are creating active exposure in real time. Misconfigurations often persist unnoticed across accounts and regions, introducing silent but critical risk. Visibility into permission to drift is also limited, as IAM roles and policies evolve, frequently leading to overprivileged identities without clear ownership.
The gaps continue with limited insight into which assets have become publicly accessible without intent, often due to temporary changes or misconfigurations that were never reversed. More importantly, even when these issues are identified, organizations struggle to understand how they translate into measurable enterprise risk. Without a normalized way to quantify and prioritize exposure, remediation and executive communication remain challenging.
This highlights a broader issue: while runtime access security is well understood, configuration-driven risk across cloud and SaaS environments remains fragmented and difficult to measure.
This creates the modern security gap: access risk is managed, but cloud misconfiguration risk remains fragmented — leaving enterprises without a unified view of their true exposure.
Posture as the defining control plane
Cloud environments are inherently dynamic.
Infrastructure is continuously created, modified, and decommissioned through automation, APIs, and distributed teams. That velocity introduces constant configuration drift—often unnoticed until it becomes exploitable.
Misconfigurations remain one of the leading causes of cloud breaches, driven by:
- Overprivileged IAM roles. Excessive permissions increase blast radius, allowing attackers to escalate privileges or move laterally across environments.
- Publicly exposed storage and APIs. Misconfigured buckets, databases, and endpoints can expose sensitive data directly to the internet.
- Weak encryption or missing controls. Inconsistent encryption settings or missing logging controls reduce visibility and increase compliance risk.
- Inconsistent policy enforcement across accounts. Multi-cloud environments often lack standardized governance, leading to gaps between intended and actual configurations.
- Unmanaged cloud costs. Unused, underutilized, or misconfigured resources inflate cloud spend — a risk CSPM surfaces alongside security findings.
At the same time, compliance expectations have evolved. Frameworks such as SOC 2, ISO 27001, and PCI-DSS now require continuous validation, not periodic audits.
The implication is clear: posture management is no longer a periodic activity. It must be continuous, contextual, and measurable.
Introducing VersaONE CSPM
Versa CSPM extends the VersaONE Universal SASE Platform to address this shift.
It provides continuous cloud posture visibility across GCP, AWS, Azure, and OCI—enabling organizations to identify, assess, and remediate misconfigurations before they translate into risk. Across AWS, GCP, and Azure, Versa supports more than 500 rules, with OCI coverage on top.
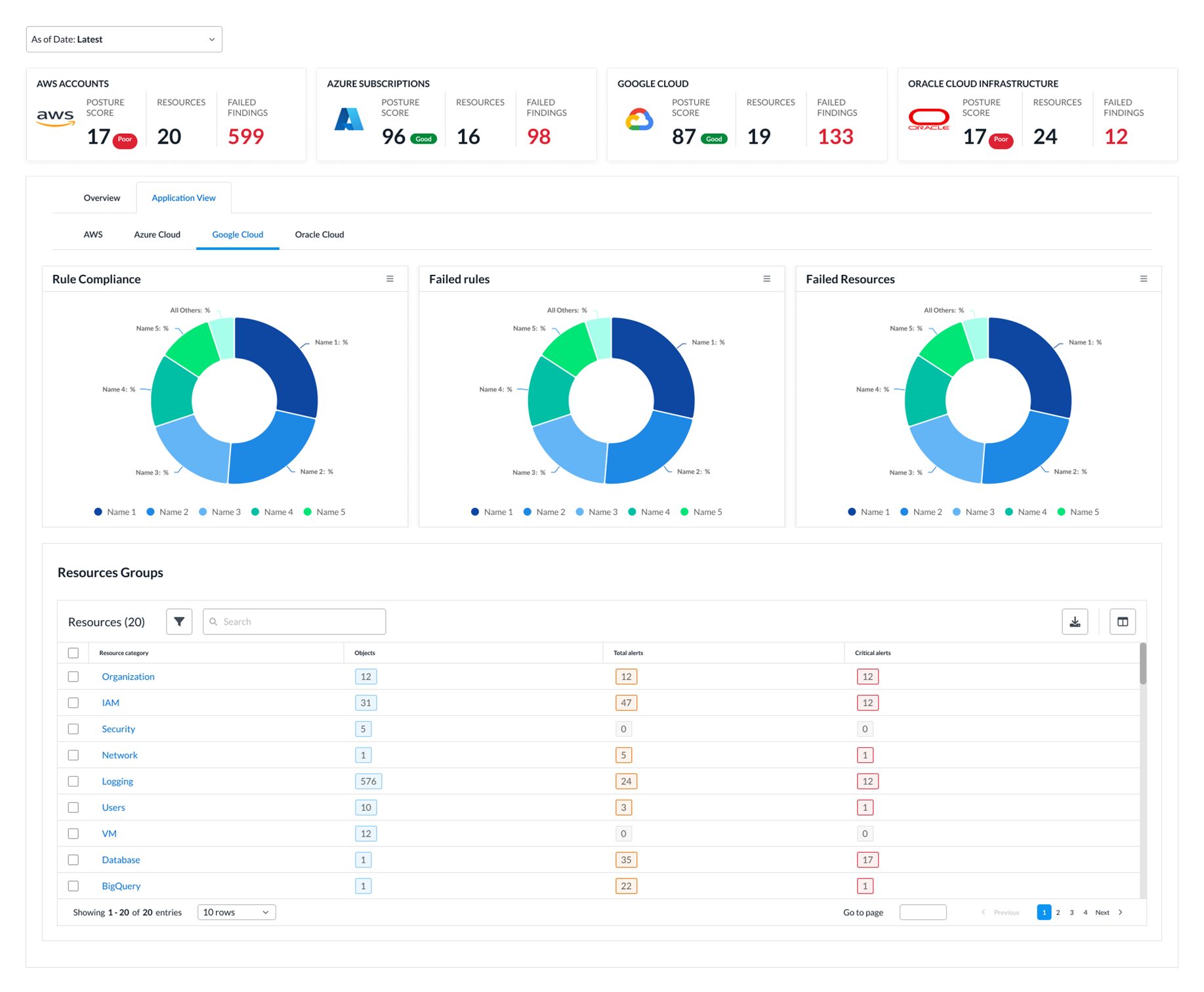
At its core, it enables security teams to:
- Continuously detect misconfigurations and policy drift. Automated evaluations identify changes in configuration state as they occur, reducing the window of exposure.
- Evaluate posture against industry frameworks (CIS, NIST, ISO 27001, SOC 2, PCI-DSS). Built-in mappings ensure that technical findings align directly with compliance requirements and audit controls.
- Discover publicly exposed resources across cloud environments. Internet-facing assets are continuously identified and flagged based on exposure risk and configuration context.
- Track identity and permission changes through IAM drift analysis. Deviations in roles and permissions are monitored over time to detect unintended or risky access changes.
- Quantify exposure through a normalized risk scoring model. A unified score translates complex findings into a measurable indicator of enterprise risk.
Instead of relying on periodic reviews, posture is evaluated automatically on a scheduled basis, reducing detection time and enabling faster response to emerging risks.
From findings to prioritized risk
Versa CSPM introduces a risk-based model that converts raw findings into actionable insights.
Each issue is evaluated based on:
- Severity of the misconfiguration
- Findings are categorized by impact level, ensuring critical issues are surfaced immediately.
- Resource exposure (e.g., internet-facing vs internal)
- Contextual awareness increases the priority of risks that are externally accessible or business-critical.
- Potential business impact
- Risk scoring aligns technical issues with operational consequences, improving decision-making.
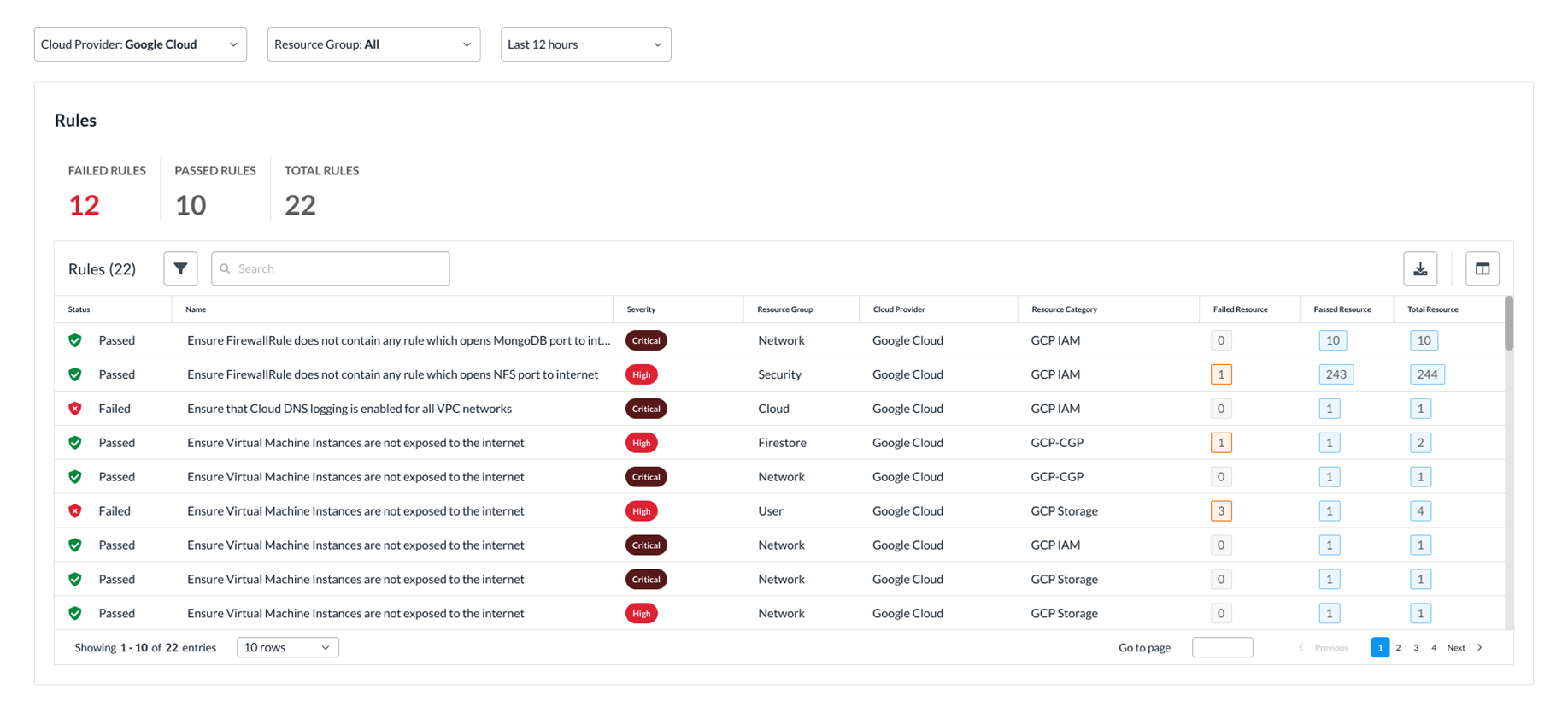
Findings are then aggregated into a unified risk score, ensuring teams focus on reducing meaningful exposure.
By combining continuous posture assessment with access protection on a single platform, Versa enables organizations to proactively identify and reduce exposure — before it becomes an incident. To sign up, click here.
Subscribe to the Versa Blog
Recent Posts
Zero Trust MCP Server: Securing the Future of Agentic AI
By Rajesh KariApril 30, 2026
The WAN for AI-era applications is becoming a single system
By Kumar MehtaApril 23, 2026


