
BrickStorm is a highly stealthy Linux backdoor designed for long-term, targeted cyber-espionage. Brickstorm is closely associated with Cyber Espionage group UNC5221, which is known for exploiting zero-days vulnerability in network edge appliances like Ivanti, F5 and MiTRE breach. Unlike commodity malware, BrickStorm is deployed post-compromise, operates largely in memory, and uses a modular architecture with custom encrypted command-and-control (C2). Its focus on Linux servers, network appliances, and embedded systems reflects a broader trend: attackers increasingly target infrastructure layers where visibility and detection are weakest.
BrickStorm exemplifies the challenges security teams face in detecting low-noise, high-discipline threats operating below the endpoint layer—and highlights the need for behavioral monitoring, memory visibility, and outbound traffic control across Linux environments.
The same can be said about any malware, but brickstorm matters as it exemplifies in articulating its attack around Unix platform and since, Unix now underpins most of the Cloud workloads, Identity Infrastructure, CI/CD Pipelines, Network and Security Appliances, it bottlenecks critical infrastructure, making it more critical for defenders.
BrickStorm is not designed to spread widely as the most malwares do or generate revenue. Instead, it enables persistent, covert access to exactly these high-value systems—often for months—while evading traditional file-based security controls, indicating clearly some state-sponsored threat actors behind the operation, that would help creator gain valuable inputs and control critical infrastructures.
BrickStorm characteristics at a glance:
🎯 Specializes in Zero-day exploits via Targeted deployment (not mass exploitation)
🧠 Memory-resident execution, to stay undetected.
🧩 Modular, on-demand capabilities, to generate low noise.
🔐 Custom encrypted C2, helping to stay hidden.
🕰️ Long dwell time, minimal forensic artifacts.
Malware has been observed in post-exploit activities, but the threat group deploying Brickstorm has been notoriously associated with exploiting zero-day vulnerabilities in network devices like F5 and Ivanti Firewalls.
Observed access vectors include:
This separation between initial access tooling and persistence tooling is common in advanced threat operations.
Key takeaway: BrickStorm is not noisy and hence require detection expertise that would help locate stealth operation. Once deployed, it blends into normal system behavior. With these characteristics it is essential organization watch out for mitigating or detecting BrickStorm by implementing
How Versa does it?
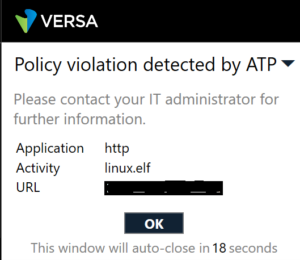
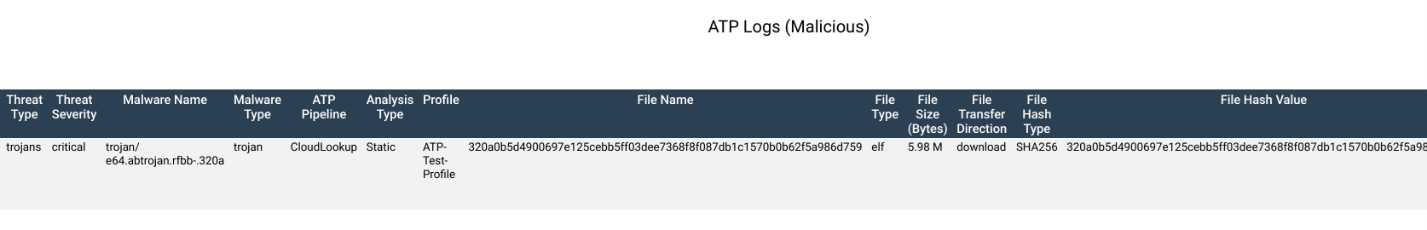
We at Versa Threatlabs, detected malware using Versa platform that closely watches malware files using Advanced Threat Protection (ATP) and also filter out any indication of zero-days using Sandbox. Also, with multiple layer protection enrolled into Versa devices, monitoring and detection of malware C2 traffic over network can be accomplished using URL Filter, IP Filter, DNS Filter and IDS/IPS.
Preventing data exfiltration
Once BrickStorm activity is detected, Versa automatically moves from visibility to prevention by enforcing inline security controls at the network edge. Suspicious outbound C2 and exfiltration attempts are blocked using a combination of Advanced Threat Protection (ATP), IPS signatures, and URL/IP/DNS filtering to stop malware communications in real time. This ensures that even if the malware executes in memory and avoids file-based defenses, its ability to beacon out and exfiltrate sensitive data is immediately disrupted through policy-driven enforcement.
[1] https://cloud.google.com/blog/topics/threat-intelligence/brickstorm-espionage-campaign
Credits – Naveen Vakkanti
Subscribe to the Versa Blog