The Ghost in the Leased Line: Unmasking MuddyWater, Surgical Cyber Arm

May 11, 2026
Author – Jayesh G.
Credits – Shyamala Pai K
In the high-stakes theater of global geopolitics, the most effective weapons aren’t always missiles; sometimes, they are just few lines of code.
MuddyWater is an advanced persistent threat (APT) group active since at least 2017, conducting cyber espionage operations across government, telecommunications, defense, and enterprise sectors globally. The group is known for leveraging a combination of publicly available tools, scripting frameworks, and “living off the land” techniques to establish and maintain long-term access within target environments data, MuddyWater operates with a level of patience and technical camouflage that has made them a persistent nightmare for global CISOs.
The Modern Mission: Geography and Intent
According to 2024 intelligence briefs from major cybersecurity firms, this actor’s current focus has narrowed to a specific concentration within a key geographic cluster. However, their operational reach has recently expanded into neighboring territories, specifically targeting entities aligned with major international security alliances.
Unlike other APT groups, their objective is rarely destruction. Instead, they seek strategic persistence by using seemingly harmless tools like remoted assistance tools. By infiltrating government ministries, telecommunications giants, and defense contractors, they provide attacker with a real-time window into the diplomatic and economic maneuvers of its rivals. As noted in recent Check Point research, the group has increasingly acted as a “reconnaissance vanguard,” mapping out sensitive infrastructure that could be neutralized in the event of a physical conflict.
Technical Deep-Dive: The Mechanics of the “Muddy” Tradecraft
What sets MuddyWater apart in recent technical reviews is their transition from custom malware to a “Living Off the Land” (LoL) philosophy. They don’t just break into a house; they use the owner’s own tools to change the locks.
1. The Infection Vector: HTML Smuggling and “Social” Phishing
MuddyWater has moved beyond simple malicious attachments. According to a 2024 Deep Instinct report, the group is now a master of HTML Smuggling.
A highly evasive malware delivery that leverages legitimate HTML and JavaScript features to bypass traditional network security controls. Unlike straightforward download from the server, malicious payloads are constructed directly on the victim’s browser.
The Tactic: They send a seemingly harmless HTML file. When opened in a browser, JavaScript on the page “assembles” a malicious payload (like a ZIP or ISO file) locally on the victim’s machine.
The Benefit: Because the malware is constructed inside the browser, it often bypasses network-level firewalls and email filters that scan for known “bad” files in transit.
2. The Persistence Framework: “Small Sieve” and PowerStats
Once inside, MuddyWater deploys their signature backdoor, Small Sieve.
Technical Detail: Small Sieve is a Python-based tool that uses the Telegram API for Command and Control (C2). By masking their traffic as encrypted Telegram messages, the data exfiltration blends perfectly with legitimate office chat traffic.
PowerStats: They continue to iterate on their PowerShell-based framework. Recent versions use “string reversal” and Base64 encoding to hide their intent from Windows Defender and other EDR (Endpoint Detection and Response) systems.
3. The “Legitimate” Intrusion: RMM Abuse
Perhaps their most effective technical trick is the deployment of legitimate Remote Monitoring and Management (RMM) tools. Analysis from Huntress and CISA has identified MuddyWater using:
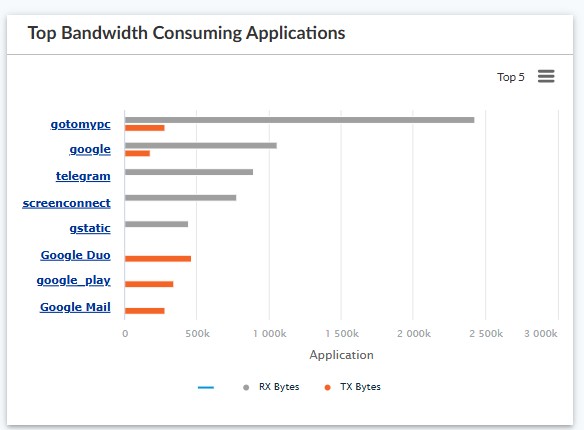
ScreenConnect (ConnectWise)
RemoteUtilities
AnyDesk
NetSupport Manager
By using these professional IT support tools, the attackers can navigate a victim’s network with full GUI access. To a security analyst, a MuddyWater hack looks exactly like a standard IT support ticket, making detection nearly impossible without advanced behavioral analytics.
4. Vulnerability Exploitation
While phishing remains their “Plan A,” MuddyWater has shown extreme agility in exploiting 1-day vulnerabilities. In the last 18 months, they have been observed scanning for unpatched ProxyShell (Exchange Server) and Log4j flaws within hours of public disclosure. They prioritize “public-facing” assets, allowing them to gain a foothold without any user interaction at all.
Why It Matters: The Future of “Grey Zone” Warfare
MuddyWater represents a shift in state-sponsored cyber activity. They are no longer just “hackers”; they are digital bureaucrats of espionage.
Recent blogs from the cybersecurity community emphasize that MuddyWater’s success isn’t due to “alien technology,” but rather to human error and administrative oversight. They thrive in the gaps between security patches and the “trust” we place in legitimate software like AnyDesk or Telegram.
As tensions in the Middle East continue to simmer, MuddyWater serves as a reminder that in the digital age, the most dangerous adversary isn’t the one who blows up the door—it’s the one who has had a copy of your keys for six months, waiting for the perfect moment to turn them.
Defensive Indicators for IT Teams:
Watch for: Unusual PowerShell execution (specifically powershell.exe -ExecutionPolicy Bypass).
Audit: Any unauthorized installation of RMM tools (ScreenConnect, AnyDesk).
Monitor: Outbound traffic to Telegram APIs (api.telegram.org) from servers that should not have internet access.
Verify: Spear-phishing attempts disguised as official “Survey” links or “Government Memos” hosted on cloud storage like OneNote or Dropbox.
How Versa One Platform’s help MuddyWater Detection and Mitigation.
- Versa helps identify application traffic, using our state of the art, AppID detection, organization can detect any unauthorized application traffic and take appropriate action. Appid covers detection of RMM tools like ScreenConnect, AnyDesk, RemoteDesktop, TeamViewer as well as messaging apps like Telegram and Signal.
- Using world class Intrusion Prevention and Detection System, any attempt to exploit underlying vulnerabilities like ProxyShell and Log4j can be blocked before any attempt to compromise target is achieved.
- Using Remote Browser Isolation (RBI), any attempts to Smuggle binaries via HTML/JavaScript can be detected, which directly feeds assembled binaries to the AV and ATP for further action.
IOCs related to the Muddywater APT
URLs
processplanet[.]org
magicallyday[.]com
api.tikavodot.co[.]il
File Hashes (SHA256SUM)
0c1c0a975ce1bee6e5eb11a2b834e1f1ec2098d6f348d3adc928f0355b3d18ce
3a22526dbf7b5534e381896de54a49c71615cc30a639c015dbca764132a5b648
131fd4ec13ae715b9babed0536dc2e615b65bb46dc2b899bda470b4d39c4f75d
d85ff06d8c06e146d067c2e7b5328cfb0faf02db165fcaad2a4129bd479c2536
6020ea571ee6e09a0500421823fd5292858bd763acc4089a56af414cfb0c82ae
930e06859b39abbd1720c11d31e6806b04ece98b3d9f13c59657295e9653beb0
50bd10fce3538698b512114e017589815d326878d847c87699768234a1d189c5
0c2513984822da4ce78208d9208e0031320edb36d123e4ed99f4f982d73e4094
ae87abdf91fd5796aedc4b90dc9fc8e7d0a2c98eacab6b6c5b6f58738455cece
cb76e43166b441bb828d12ccf529c2ec0a12c7c5af56618028ff963d1c9de5c9
27723a3f6febc6e95cdcf5ca868feafb32dfbd6f9adc30d03a52b4cd89b3e67f
fcd2a678a276d95654ab8750318914baf02ae49fccf94de9bd3a50bc97614e28
34170ec31f586bc4854cffa01cd794b7046b1384cc4610670be9bd25f6add227
ba5386a12d7e7df0cf34169f264aa3a3c406f5a54a5c7febe13bc59009c86ce7
0a216f6543c61f95cb8b320b46bcd3f767d341f0d9200353b889407f6af4ab09
10da2be34cd7a895c3f3fc785ce40c73c1965b6853abc237d7af184677e71202
97bc1aa8a1671a806a35331588e946efd595aed00207beaf0af4752fa9114e94
References
[1] https://github.com/eset/malware-ioc/tree/master/muddywater
Subscribe to the Versa Blog
Recent Posts
Zero Trust MCP Server: Securing the Future of Agentic AI
By Rajesh KariApril 30, 2026


