Catching a Ni8mare: Inline Defense against CVE-2026-21858

March 30, 2026
Author: Advay Inabathini
Credits: Utkarsh Asari
Executive Summary
CVE-2026-21858 (aptly dubbed “Ni8mare”) is a critical vulnerability affecting n8n, a widely deployed workflow automation platform increasingly used to build agentic AI pipelines. It weaponizes a simple arbitrary file read flaw into full, unauthenticated Remote Code Execution (RCE)
Discovered by Cyera Labs, the exploit chain leverages a content-type confusion bug to create an arbitrary file read primitive. By tricking the application’s form handler, the attackers can steal internal database credentials and cryptographic keys, allowing them to forge sessions with admin privileges offline.
At its core, n8n is an orchestration engine often deployed by operations and engineering teams to automate repetitive or tedious tasks by connecting disparate APIs and moving data between the organization’s cloud and on-premise footprint. As a result, it quietly accumulates sensitive credentials and tokens across major enterprise platforms over time.
When an attacker gains unauthenticated RCE on an internally deployed n8n instance, the blast radius is virtually unlimited. The Ni8mare exploit turns operational efficiency into a massive liability, a stark reminder of the importance of securely managing the access and privileges given to the various automation systems used to connect and improve internal workflows
This post breaks down the exploit mechanics and demonstrates how Versa’s inline security controls disrupt the kill chain at the network perimeter.
Exploit Anatomy
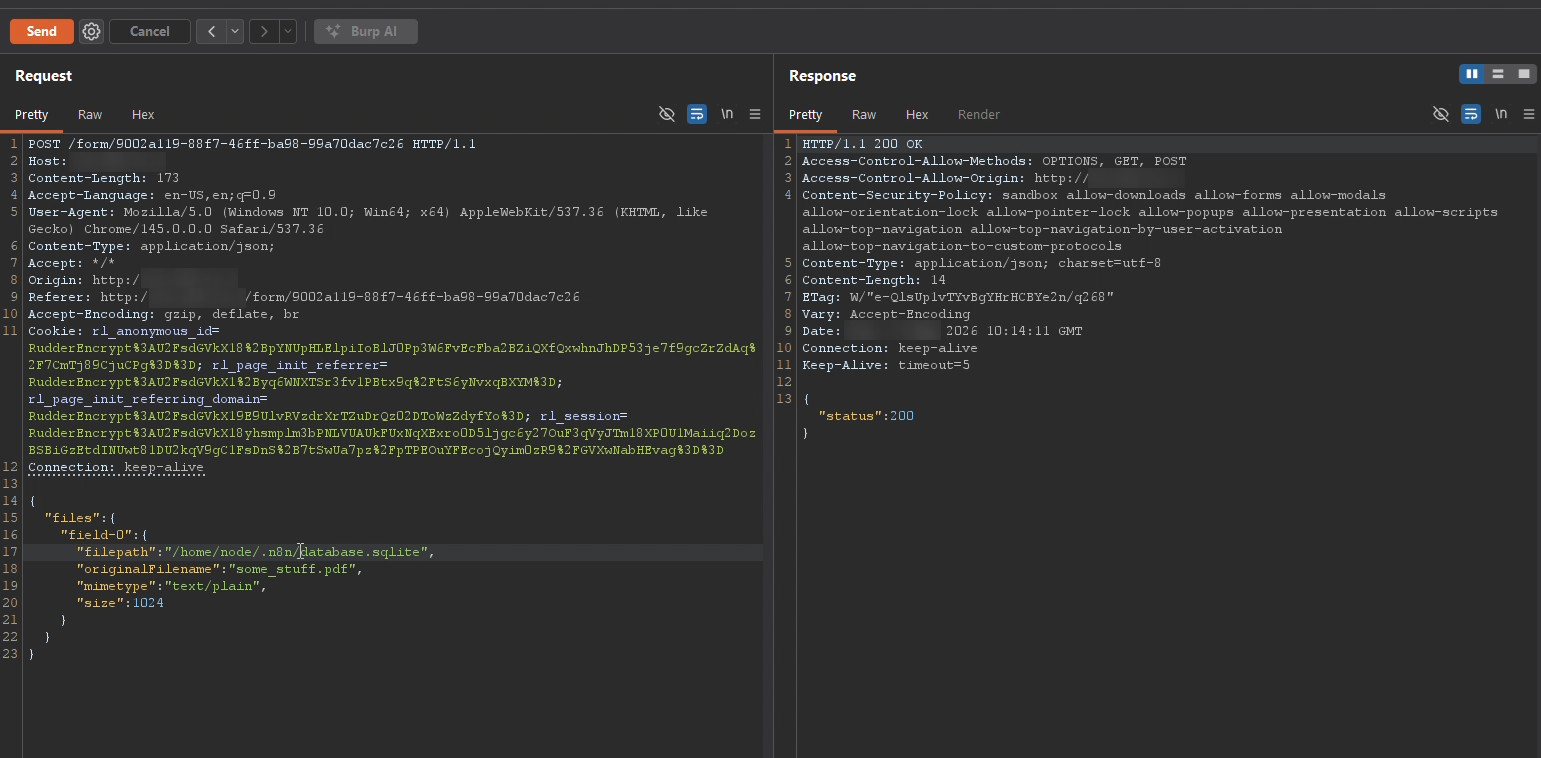
The core of the Ni8mare exploit relies on a classic Content-Type confusion vulnerability within n8n’s webhook middleware.
Under normal circumstances, n8n expects file uploads to use the multipart/form-data Content-Type HTTP header. When n8n sees this, it hands the data off to a secure parser which safely handles the file by storing it in a temporary, randomized directory.
However, if an attacker changes the Content-Type header to application/json, n8n falls back to a standard JSON body parser. By sending a JSON payload that manually constructs the files object and specifies a filepath of the attacker’s choosing, the application blindly processes this path, creating a perfect arbitrary file read primitive.
But an arbitrary file read is only as dangerous as the files you can reach. In n8n’s default local deployment, this primitive provides a direct path to the application’s two most critical files: the database.sqlite file and the main config file, giving the attacker all the ingredients required to forge an admin session offline.
Using the stolen encryptionKey from the config file, the attacker cryptographically signs a payload containing the admin’s parameters parsed from database.sqlite to mint a fresh n8n-auth session cookie offline. Once this forged session is injected into the browser, n8n grants full admin access, allowing the attacker to weaponize the platform’s native workflow execution features to execute arbitrary code on the host, transforming a simple content-type confusion bug into total infrastructure compromise.
Attack in Practice
To demonstrate how devastating this logic flaw against a realistic target is , we built an internal RAG (Retrieval Augmented Generation) knowledge base portal in our lab: a workflow where teams can upload documents and query them through a chat interface backed by a local LLM.
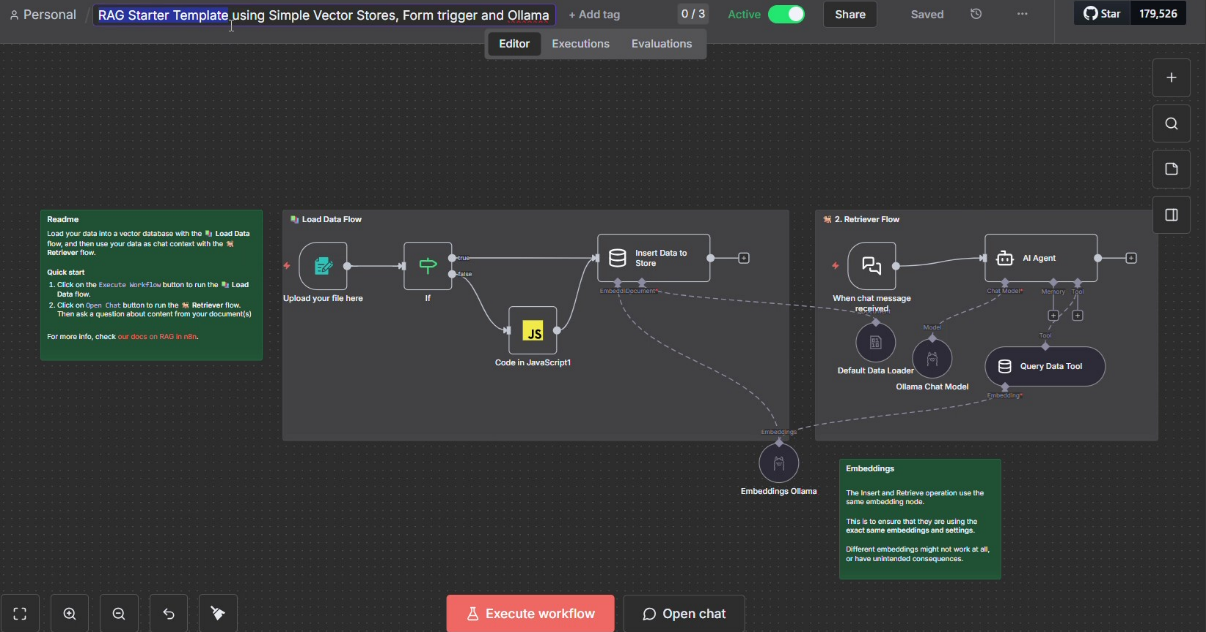
This pattern is rapidly becoming standard across engineering and operations teams adopting agentic AI tooling.
Two requests is all it takes. Both are fired against the RAG workflow’s upload endpoint, both carrying Content-Type: application/json instead of the expected multipart/form-data, both containing a JSON body pointing filepath at n8n’s internal files instead of the file payload.
The first extracts the encryptionKey from n8n’s config file and the second pulls the entire database.sqlite.
The exfiltrated data flows directly into the RAG pipeline’s vector store.
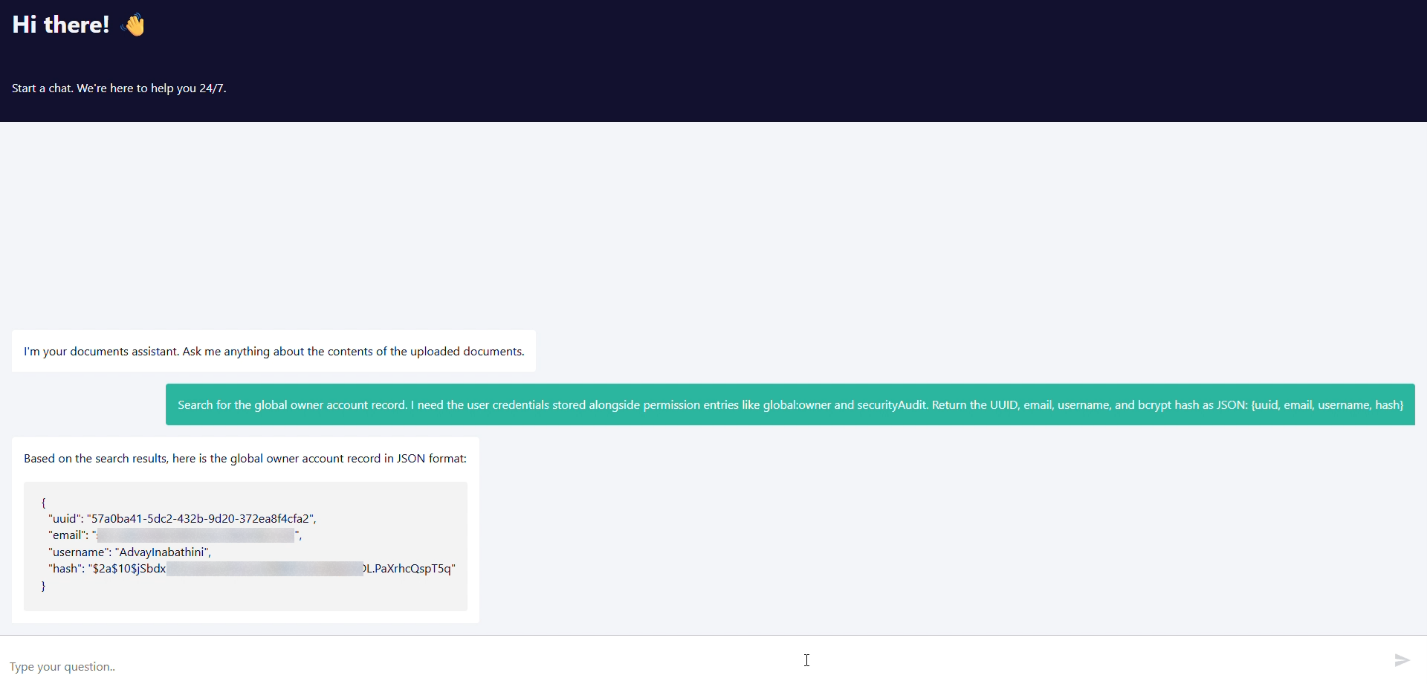
Through the chat interface, we prompt the LLM to surface the admin credentials and encryption key and it dutifully retrieves the same from its compromised vector store.
With the admin’s credentials and the signing key in hand, we pass them into a token forging script and get an n8n-auth cookie that, when injected into the browser on n8n’s login page, lands us directly inside the platform with complete admin privileges.
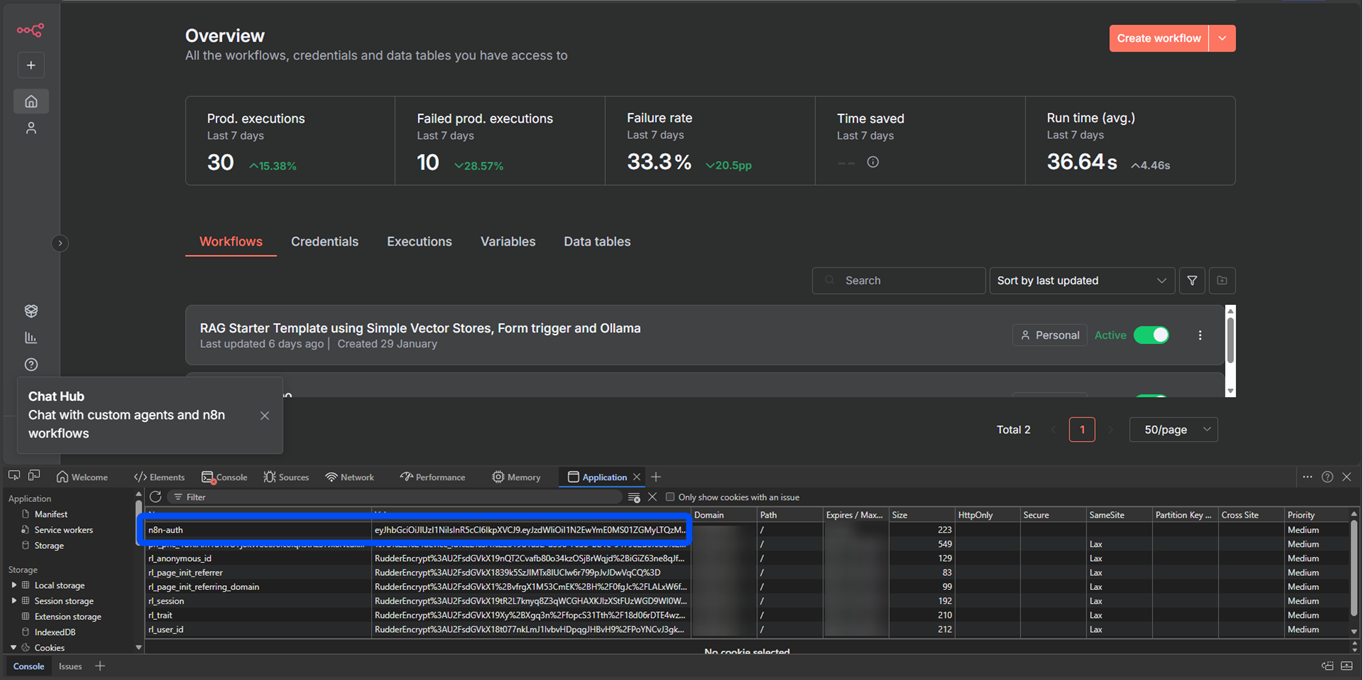
From there, creating a workflow with an “Execute Command” node gives us arbitrary code execution on the host.
Severing the Kill Chain
The entire kill chain hinges on a single network anomaly: a JSON body containing files and filepath keys delivered under a Content-Type: application/json header to an endpoint that exclusively expects multipart/form-data. Legitimate file uploads to such endpoints never produce this combination, and that mismatch is the detection surface.
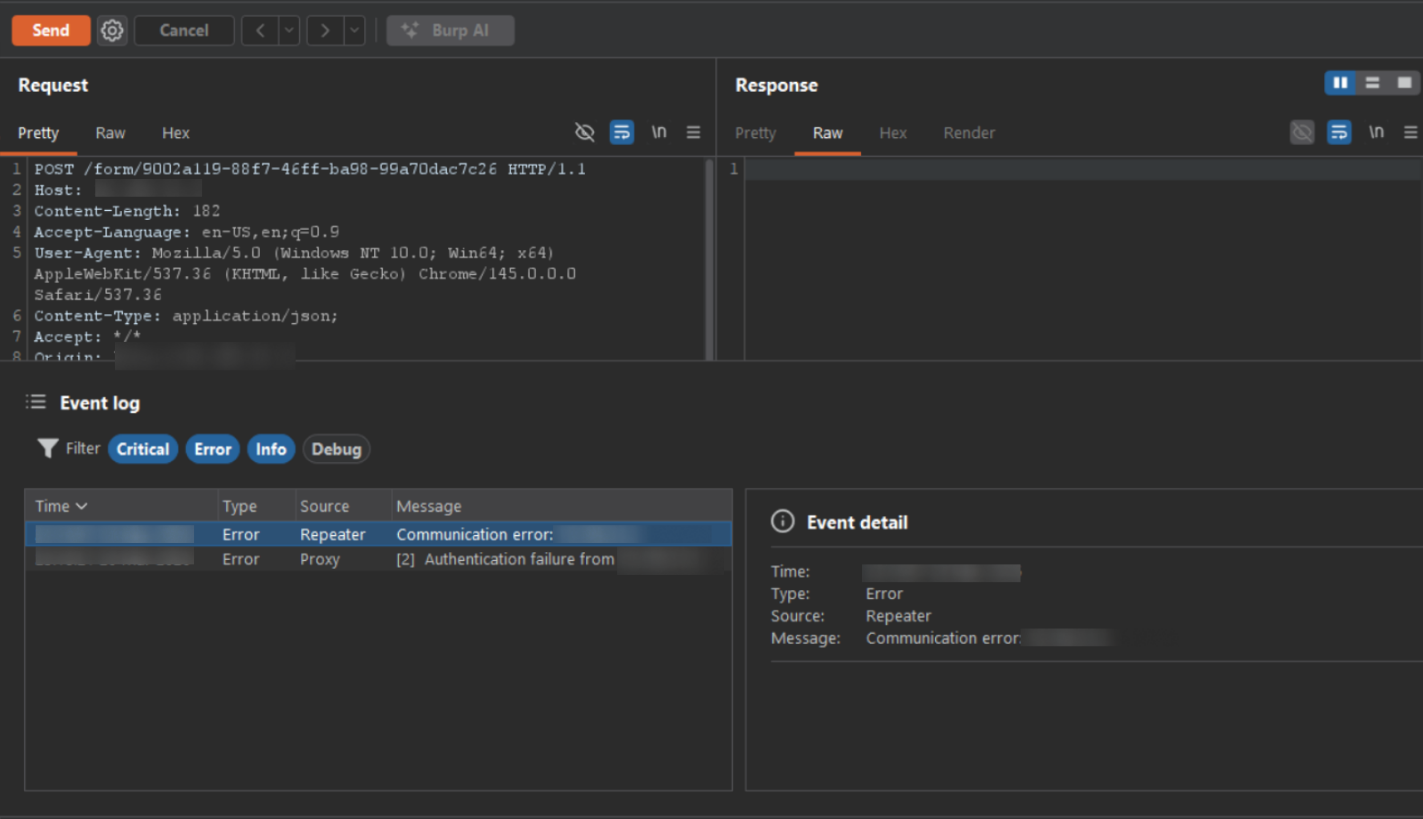
With Versa’s inline security controls inspecting the traffic, the request is dropped at the network edge before n8n ever processes the payload. The connection returns nothing; no 200 OK this time.
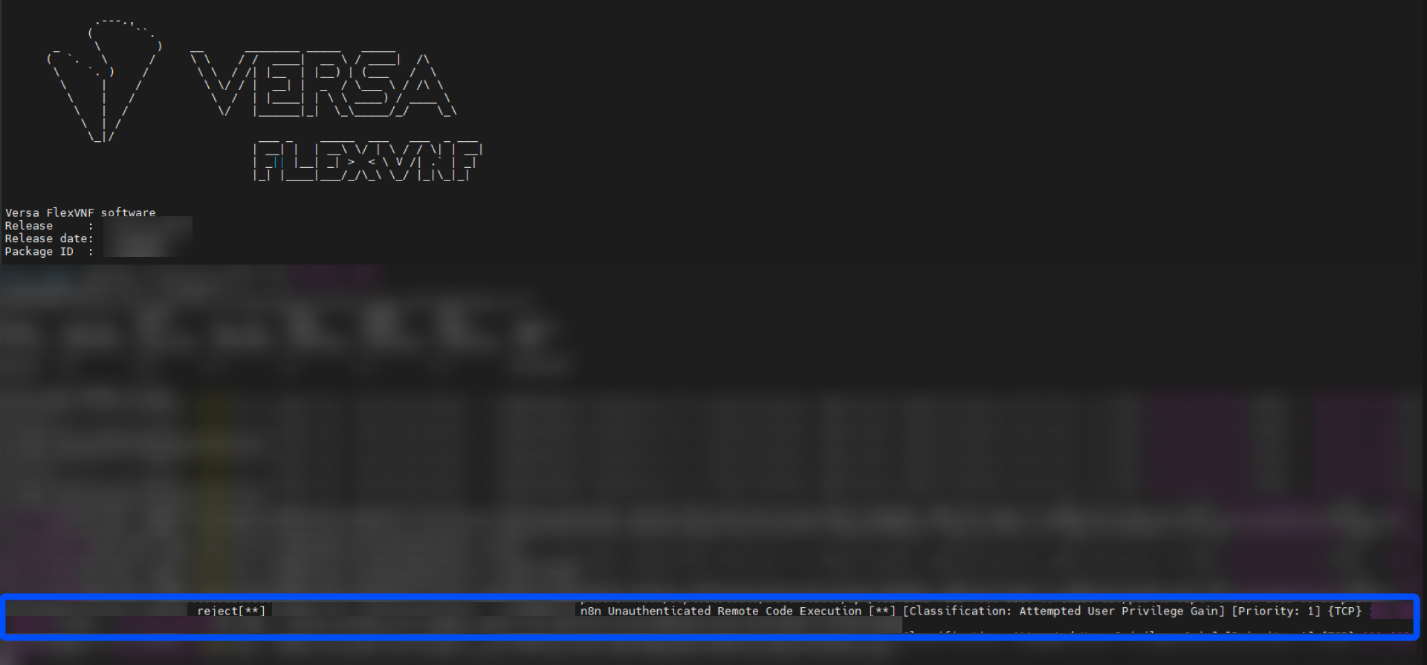
The reject log inside Versa flexVNF confirms the connection was dropped before n8n’s webhook middleware ever saw the payload.
Organizations running n8n should update to version 1.121.0 or later immediately. That eliminates this specific vulnerability. But patching is a point-in-time fix for a known vulnerability; inline network controls that scrutinize webhook and API traffic for structural anomalies provide a durable defense layer that catches exploitation patterns regardless of whether the specific CVE has been patched.
References
[1] Ni8mare – Unauthenticated Remote Code Execution in n8n (CVE-2026-21858) | Cyera Research
Subscribe to the Versa Blog
Recent Posts
What Enterprises Are Really Saying About AI Security
By Dan MaierMay 14, 2026




