Detect emerging threats with AI-powered behavior analysis
Versa User and Entity Behavior Analytics (UEBA) leverages AI-driven analytics and security research to detect and alert you to anomalous activities that may signal insider threats, compromised accounts, or advanced persistent threats (APTs). By identifying unusual behavior patterns in real-time, Versa UEBA becomes a critical component of your layered security strategy, helping you stay ahead of potential threats.
Learn more
Benefits
Discover relationships
Discover common attack patterns & relationships between various threat actors and entities in your network.
Detect previously unknown threats
Identify new and emerging attack methods by analyzing behavior patterns in security and network telemetry.
Detect threats faster
Identify anomalies in real time, ensuring prompt alerts and rapid response to potential security incidents.
Reduce false positives
AI-driven analysis reduces the number of false positives, allowing your security team to focus on real threats.
Continuous monitoring
Versa UEBA continuously monitors network traffic, user behavior, and system logs to baseline nominal behavior and detect unusual activities that could indicate potential security breaches. This includes application performance anomalies or latency discrepancies between locations. Entities analyzed include users, laptops, phones, IoT devices, and more.
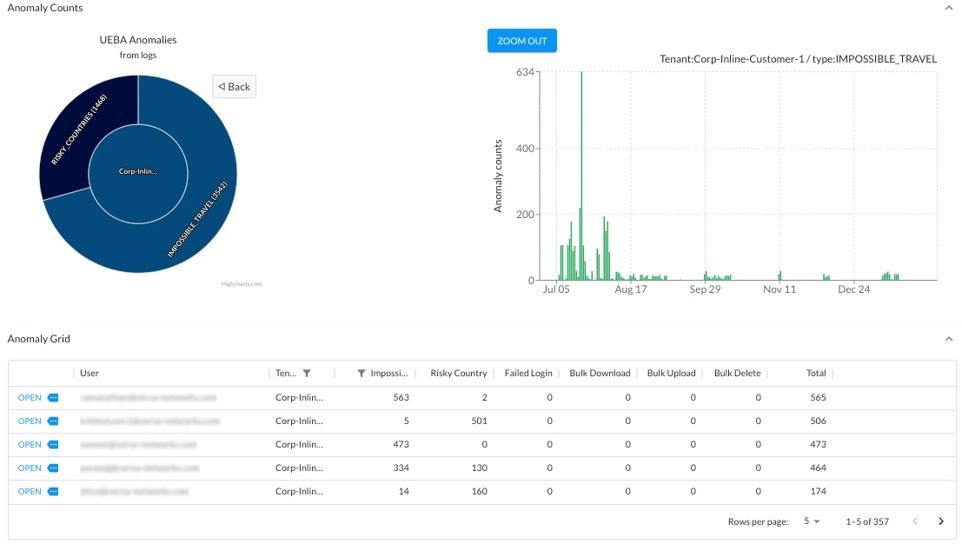
Anomalous behavior detection
Some of the common anomalous behaviors identified by Versa UEBA include infrequent destinations, impossible travel behavior, bulk deletions, bulk downloads, and suspicious access from different devices. In addition, Versa UEBA identifies behaviors that significantly deviate from the baseline of normal activities that the service maintains, to help identify new and emerging attack patterns and techniques.

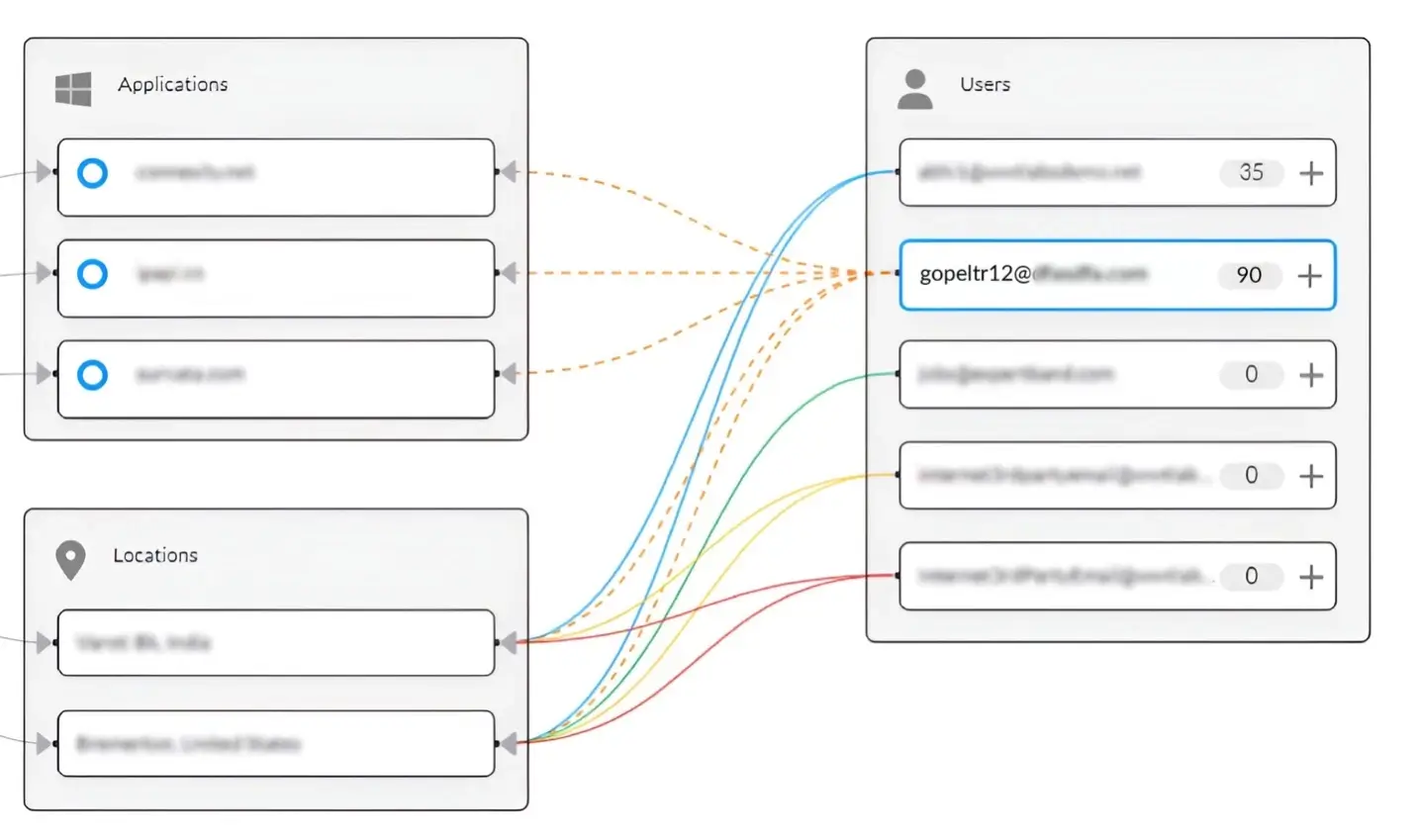
Visualize security incident relationships
Versa UEBA uses social graphs to detect anomalies, determine the blast radius and quickly find the root cause of a security incident. Security teams can easily visualize risk and accelerate forensic analysis to drill down into the relationships between users, devices, and apps/resources.
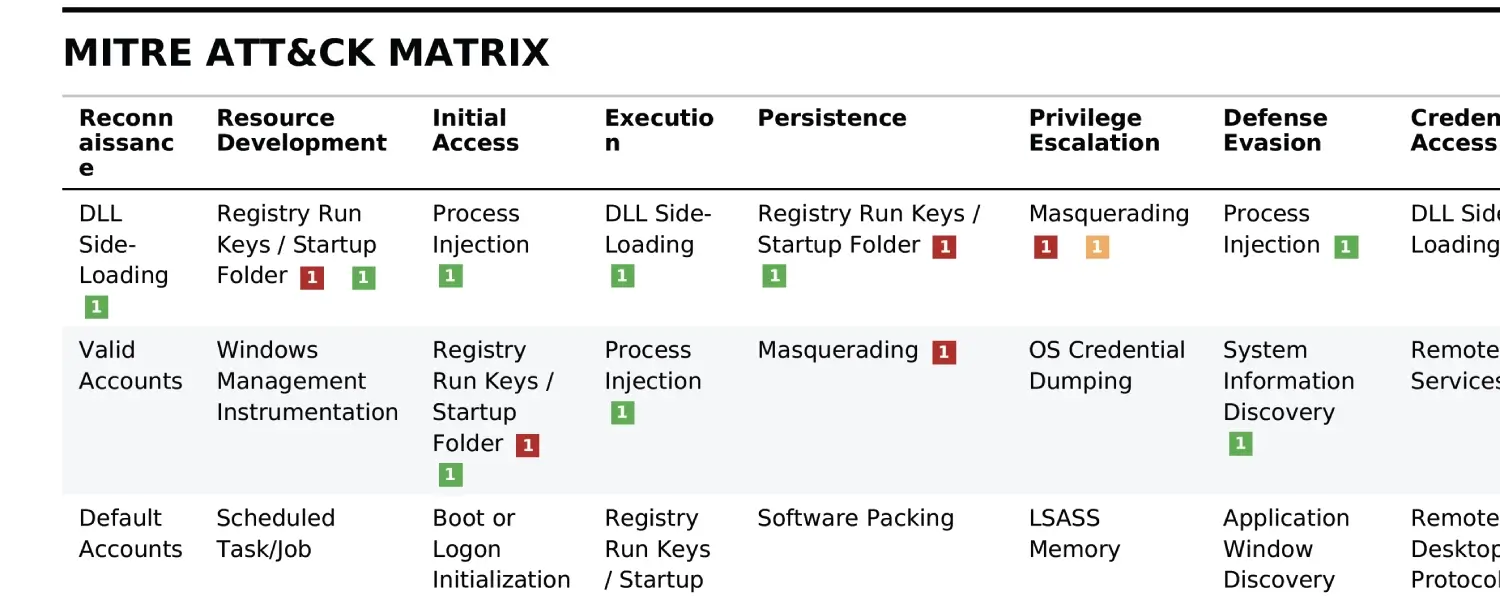
MITRE ATT&CK Integration
To enhance the fidelity of threat detections and accelerate incident response, Versa UEBA includes detailed insights into adversary behaviors from an expanded library of attack behaviors aligned to MITRE ATT&CK TTPs.
Insider threat detection
Identifies employees who may pose a security risk through unauthorized access or data exfiltration
Compromised account detection
Detects signs of account compromise, such as unusual login patterns or data access.
Regulatory compliance
Helps organizations meet various regulatory requirements by providing detailed activity logs and reports.