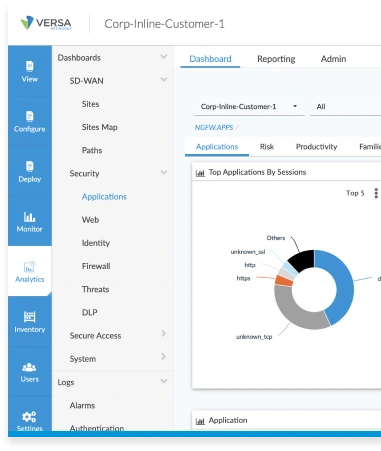
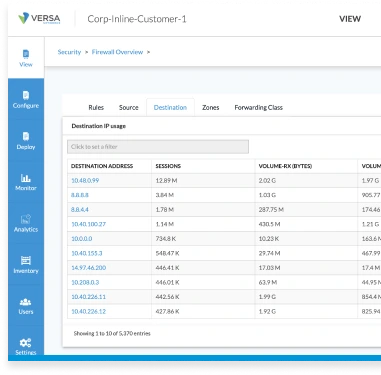
AI-powered defenses
Complete suite of threat protection, data protection, and secure access capabilities.
Easy management
Simplified security management through a unified platform.
Enhanced UX
Seamless security without performance trade-offs for your users.
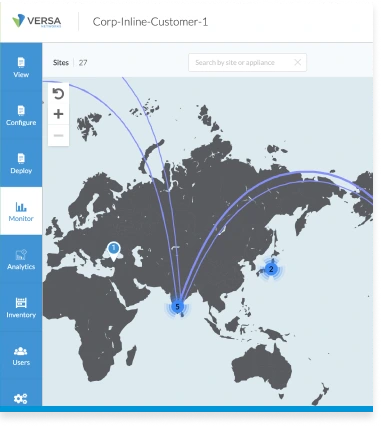
Scalable solution
Grows with your business needs, ensuring consistent protection.