Versa Security Bulletin: Palo Alto Networks PAN-OS GlobalProtect Zero-Day Vulnerability under Active Exploitation

April 19, 2024
CVEs: CVE-2024-3400;
Summary
Recently Palo Alto Networks announced a critical vulnerability in their PAN-OS software used in their GlobalProtect VPN Gateway, which is a feature in the PAN-OS Firewall. The discovery and public disclosure of the vulnerability and fixes timeline is currently as follows:
- Volexity first discovered the PAN-OS attack on April 10, 2024 at one of its network security monitoring (NSM) customers, and on April 11, 2024 subsequently learnt that another NSM customer was compromised by the same threat actor.
- Palo Alto Networks was then notified by Volexity that a zero-day vulnerability in its GlobalProtect Gateway was under active exploitation in the wild.
- On April 12, Palo Alto Networks publicly disclosed that a zero-day critical vulnerability CVE-2024-3400 in its GlobalProtect Gateway is under active exploitation by threat actors. The vulnerability was assigned a CVSS score of 10.0, indicating maximum severity i.e. critical score.
- In parallel, Palo Alto Networks issued a security advisory on CVE-2024-3400 that included information regarding vulnerable configurations, workarounds and mitigations, as well as a timeline for a fix for impacted PAN-OS versions.
- On April 15, Palo Alto Networks provided hotfixes for affected PAN-OS firewalls, clarified workarounds and mitigations, and advised that a software fix to PAN-OS was coming.
- On April 16, Palo Alto Networks provided a new threat prevention ID to workarounds and mitigations.
- On April 18, Palo Alto Networks clarified the vulnerability title and description in the advisory to “Arbitrary File Creation leads to OS Command Injection Vulnerability in GlobalProtect”.
Under active exploitation, details surrounding the PAN-OS vulnerability and configurations vulnerable to attack are frequently changing. For the most current guidance from the vendor on product and mitigation guidance, exploit status, vulnerable configurations and PAN-OS software fixes availability, customers should refer to the Palo Alto Networks security advisory.
CISA has alerted users and administrators to apply the current mitigations for CVE-2024-3400 and update software when Palo Alto Networks makes it available. We continue to monitor the situation and will provide updates as more information is made available.
Details of the Vulnerability
Specifically, a critical command injection vulnerability (arising from arbitrary file creation) in the GlobalProtect feature of Palo Alto Networks PAN-OS firewall software PAN-OS versions 10.2, 11.0, and 11.1 and distinct feature configurations can be exploited by an unauthenticated user or attacker to execute arbitrary code with root privileges on the firewall. Command injection vulnerabilities typically occur when data enters the application from an untrusted source; further, the data is part of a string that is executed as a command by the application; and by the executing the command, the application gives an attacker a privilege or capability that the attacker would not otherwise have.
We have learnt that exploitation of this vulnerability can be automated. Palo Alto Networks initially said that this vulnerability impacts Palo Alto Networks firewalls that have the configurations for both GlobalProtect gateway (Network > GlobalProtect > Gateways) and device telemetry (Device > Setup > Telemetry) enabled. It is now clarified by the vendor that device telemetry does not need to be enabled for the software to be exposed to the attack.
Exploitation in the wild
While Palo Alto Networks has started releasing hotfixes on April 15 to secure unpatched firewalls exposed to attacks, the vulnerability has been exploited in the wild as a zero-day since March 26th to backdoor firewalls using Upstyle malware, pivot to internal networks, and steal data by a threat group believed to be state-sponsored and tracked as UTA0218.
Palo Alto Networks has also reported that they are aware of an increasing number of attacks actively exploiting this vulnerability. Proof of concepts for this vulnerability have been publicly disclosed by third parties. Threat researchers have found over 82,000 PAN-OS firewalls vulnerable to CVE-2024-34000 attacks, 40% of which were in the United States. In response to the attacks, CISA issued an alert and added CVE-2024-3400 to its Known Exploited Vulnerabilities (KEV) catalog on Friday, ordering U.S. federal agencies to secure their devices within seven days by April 19th.
In addition, over the past 5 days (from April 15 – 19), 16 unique IP addresses tagged as PALO ALTO PAN-OS CVE-2024-3400 RCE ATTEMPT have been observed attempting to exploit CVE-2024-3400 according to GreyNoise Intelligence. See list of observed IP addresses here.
Interim Guidance
In an update to their advisory on April 16, Palo Alto Networks warned that previously shared mitigations have been found to be ineffective at protecting devices from the vulnerability.
“Earlier versions of this advisory, disabling device telemetry was listed as a secondary mitigation action. Disabling device telemetry is no longer an effective mitigation,” reads an update to Palo Alto Networks security advisory.
“Device telemetry does not need to be enabled for PAN-OS firewalls to be exposed to attacks related to this vulnerability.”
Therefore, the best solution is to install the latest PAN-OS software update to fix the vulnerability. Customers should continue to monitor Palo Alto Networks security advisory for the latest updates and product guidance.
Versa Networks Protections for PAN-OS GlobalProtect Vulnerability
The Security Research Team in Versa Networks plays a crucial role in protecting customers from vulnerabilities. Versa’s proactive approach in identifying, developing, and implementing detection and protection rules is vital in blocking vulnerability exploits and helping our customers maintain strong security defenses against both known and zero-day attacks.
Versa Networks has identified the issues and added 2 SIDs (Security IDentifier) to protect customers against the PAN-OS CVE exploit and mitigate any threats arising from exposure. The signatures are available in our latest offering of Security Package (SPACK) version 2152:
| SID (Signature Identifier) | CVE |
|---|---|
| 1000019917, 1000019921 | CVE-2024-3400 |
The signatures are part of the Versa recommended vulnerability profile and customers will automatically get protection. Versa recommends that customers running a custom vulnerability profile select and activate the signature to get protection. Customers can visit our Support Center to obtain more information on SPACK 2152 and follow the forum.
Versa Networks customers benefit from enhanced protection provided through our Secure Service Edge (SSE) solution. Enterprise-wide protections from zero-day attacks are provided by:
-
Versa Zero Trust Network Access (ZTNA)
– Versa ZTNA, a cloud delivered VPN–replacement solution, delivers Zero Trust based secure remote access for employees. With this solution, remote employees can securely connect to private applications anywhere, anytime. Versa ZTNA extends to the local on-premises environments, and Zero Trust based secure on-premises access is similarly enforced for users in the branch, campus or data center, limiting lateral movement of threats inside the network.
-
Versa Secure Internet Access (VSIA) with Secure Web Gateway, URL filtering and DNS security
– Cloud-managed and cloud-delivered, VSIA secures enterprise sites, home offices, and traveling users accessing distributed applications and the Internet without compromising security or user experience. URL filtering with IP reputation inspects all incoming and outgoing enterprise traffic for malicious exploits and known malicious domains, including those associated with the vulnerabilities, and will block associated IOCs.
-
Versa Next Generation Firewall(NGFW) with IPS and Advanced Threat Prevention
– Provides comprehensive security coverage and can help to block attacks arising from the vulnerabilities via security packs and sandboxing, together with other elements within the VSIA product offering.
-
Versa Data Loss Prevention (DLP) – Network DLP
scanning of email and inline Web, SaaS, private and Internet applications detects and prevents exfiltration of sensitive information via the network. Versa Network DLP monitors, detects and blocks illegal or unauthorized exfiltration of data while it is in motion across the network, using multiple scanning methods across many discrete content types.
Conclusion
In recent years, the cybersecurity threat landscape has evolved dramatically. We are seeing increased participation from state-sponsored threat actors, and the application of AI has only increased the level of sophistication in attacks. In this environment, legacy VPNs both standalone and available as features in legacy firewalls pose a serious threat to customer networks, as we have seen with the recent spate of critical vulnerabilities in Ivanti/Pulse Secure VPN, Citrix, and Fortinet FortiOS appliances, and now PAN-OS GlobalProtect. Below we list the critical/severe VPN vulnerabilities that were recently disclosed:
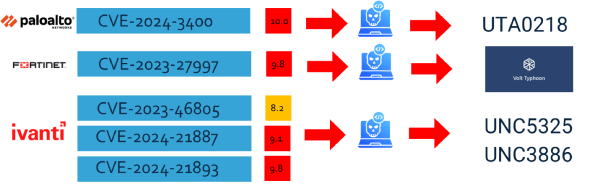
Built on legacy architectures, these products actually increase the attack surface and provide fertile ground for hackers. Here are some architectural differences between VPN and Zero Trust-based network access that can help to explain why we are seeing so many critical zero-day vulnerabilities in VPNs:
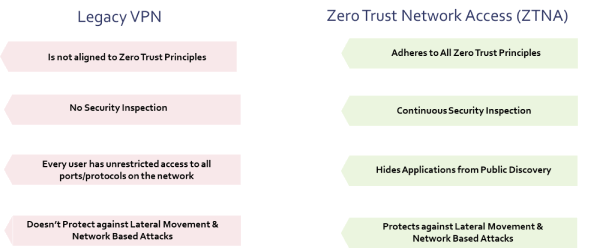
Customers can protect their networks by replacing legacy VPNs with a Zero Trust based approach to secure access, such as that provided by Versa ZTNA, and embrace a Secure Service Edge (SSE) architecture that consolidates security, reduces lateral movement and blind spots, and enforces least privilege access policies for maximum protection against attacks.
Indicators of Compromise (IOCs)
Below is the complete list of IP and malicious files involved with their hashes:
172.233.228.93
66.235.168.222
144.172.79.92
198.58.109.149
3de2a4392b8715bad070b2ae12243f166ead37830f7c6d24e778985927f9caac
35a5f8ac03b0e3865b3177892420cb34233c55240f452f00f9004e274a85703c
755f5b8bd67d226f24329dc960f59e11cb5735b930b4ed30b2df77572efb32e8
adba167a9df482aa991faaa0e0cde1182fb9acfbb0dc8d19148ce634608bab87
c1a0d380bf55070496b9420b970dfc5c2c4ad0a598083b9077493e8b8035f1e9
fe07ca449e99827265ca95f9f56ec6543a4c5b712ed50038a9a153199e95a0b7
96dbec24ac64e7dd5fef6e2c26214c8fe5be3486d5c92d21d5dcb4f6c4e365b9
448fbd7b3389fe2aa421de224d065cea7064de0869a036610e5363c931df5b7c
e315907415eb8cfcf3b6a4cd6602b392a3fe8ee0f79a2d51a81a928dbce950f8
161fd76c83e557269bee39a57baa2ccbbac679f59d9adff1e1b73b0f4bb277a6
References
Threat Brief: Operation MidnightEclipse, Post-Exploitation Activity Related to CVE-2024-3400
CVE-2024-3400 PAN-OS: OS Command Injection Vulnerability in GlobalProtect (paloaltonetworks.com)
Zero-Day Exploitation of Unauthenticated Remote Code Execution Vulnerability in GlobalProtect (CVE-2024-3400)
Palo Alto Networks Releases Guidance for Vulnerability in PAN-OS, CVE-2024-3400
Zero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
https://www.bleepingcomputer.com/news/security/exploit-released-for-palo-alto-pan-os-bug-used-in-attacks-patch-now/
https://github.com/noperator/panos-scanner?tab=readme-ov-file
POC:
Subscribe to the Versa Blog
Recent Posts
Versa SASE Fabric
By Matthew BrooksMay 26, 2026
What Enterprises Are Really Saying About AI Security
By Dan MaierMay 14, 2026



